You’ve probably seen it: a VPN app proudly advertises AES-256 encryption but gets blocked the second a user connects from school, work, or a country with active censorship. They’re encrypted, but offline.
Here’s why: no modern censor needs to “break” your encryption. They just detect your tunnel and shut it down at the network edge. Firewalls watch for VPN fingerprints — handshake ciphers, TLS extension orders, packet size patterns, and static ports. It’s deep packet inspection (DPI) in the real world.
If you’re launching or scaling a white label VPN, this is where things get serious. A brand that promises “private, unrestricted access” but fails the moment someone actually needs it? That’s churn you never get back. Refunds. Negative reviews. Support tickets stacking up because your tunnel was too obvious.
What VPN Obfuscation Really Means?
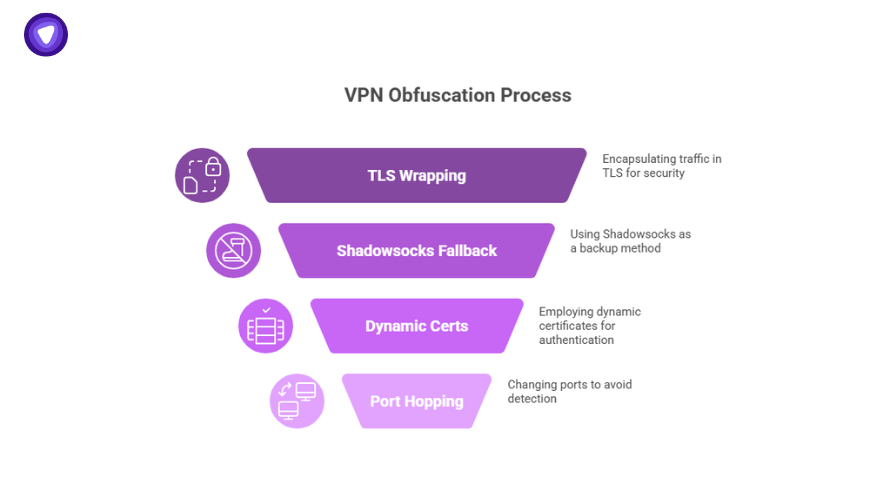
Obfuscated VPN just means a tunnel that’s invisible to censorship. When you obfuscate VPN traffic, you strip out the fingerprints DPI relies on. The best stealth setups use layered tricks: TLS wrapping, Shadowsocks fallback, dynamic certs, port hopping.
If you’re asking what is obfuscated VPN, think of it as a cloak that turns encrypted packets into something that looks like everyday HTTPS. Censors risk breaking real websites if they block you.
Many search for free VPN obfuscation solutions but miss the catch: stale IPs, reused keys, and zero QA. Free stealth is easy to spot and block. Real obfuscation is a living system that updates daily.
Obfuscated VPN vs. Double VPN: The Real Difference
| Feature | Obfuscated VPN | Double VPN |
|---|---|---|
| What it does | Hides tunnel signature to beat DPI | Routes traffic through multiple hops |
| Stops detection? | Yes — if properly managed | Tunnel still visible |
| Adds privacy layers? | No — focuses on hiding | Yes — splits entry and exit hops |
| Impact on speed | Low latency if optimized | Higher latency |
| Best used for | Beating censorship & staying online. | Extra privacy & jurisdiction split. |
| Smart approach | Combine both for max stealth & privacy where needed. | |
What a Good Obfuscated VPN Backbone Looks Like?
Anyone can say they offer “stealth.” Actually delivering it is where most providers fall short. If you’re building a VPN brand that people trust in challenging markets, you need more than a checkbox feature. You need a backbone that can adapt when detection methods change. Here’s what sets real obfuscation apart from marketing hype.
Does Your Stealth System Do This?
Dynamic Exit IP Pools
One of the easiest ways for blocklists to shut you down is by catching stale exit IPs that thousands of users share for weeks or months. A solid obfuscated VPN backbone constantly rotates its exit IPs, refreshing them before they become a liability. This rotation makes it much harder for censors to build reliable blocklists that stick. If your white label VPN isn’t doing this, your users will feel it when their connection drops for no clear reason.
Cert and Port Rotation
A tunnel’s handshake is like its fingerprint. If you reuse the same certificates and run on the same ports day in and day out, DPI tools will find you. A strong obfuscation stack updates certs automatically and shifts port ranges so the signature of your tunnel keeps changing. This is one reason why cheap or free stealth solutions get flagged: they’re static. Good stealth is dynamic by default.
Smart Regional Toggles
Not every user needs stealth all the time. Some regions don’t inspect VPN traffic aggressively — others block it daily. The best VPN obfuscation setups include region-aware toggles. This means stealth is turned on when it’s actually needed, so users aren’t stuck with the extra overhead when they don’t need it. It’s the balance between staying hidden and keeping performance as high as possible.
Ongoing QA to Handle Evolving DPI
Deep packet inspection methods change constantly. That means your obfuscation stack has to evolve too. Good providers treat stealth like a living system, not a one-time patch. They run regular QA tests to catch new detection methods, update handshake obfuscation, and swap out protocols if needed. This level of maintenance is exactly why a managed solution like PureVPN’s white label is miles ahead of DIY or static setups.
How Deep Packet Inspection Finds You?
How Deep Packet Inspection Finds You
Click each trap card to see how weak stealth can get caught.
Tip: Change your handshake settings often.
Tip: Rotate your ports to stay hidden.
Tip: Refresh them regularly.
Tip: Switch protocols if needed to blend in.
Deep packet inspection (DPI) is what makes or breaks a VPN in restrictive regions. It’s not enough to have strong encryption — modern firewalls don’t need to crack your AES keys.
1. JA3 Fingerprinting of TLS Handshakes
Modern DPI engines run JA3 hashes to match your VPN’s TLS handshake. They check your ciphers, TLS extensions, and the order they appear. A standard OpenVPN handshake is predictable — firewalls use that signature to block you. Smart VPN obfuscation scrambles this handshake so you don’t stand out.
2. Static Port Usage
If your tunnel always uses the same port — like OpenVPN’s classic 1194/UDP — you’re giving censors an easy target. Many free VPN obfuscation scripts fail here. A VPN with obfuscated servers rotates ports dynamically to break these patterns.
3. Packet Size and Burst Timing
DPI doesn’t just peek at headers — it watches packet flow. Normal HTTPS traffic has a mix of sizes. Basic VPN tunnels send packets in uniform sizes or bursts that scream “encrypted tunnel.” Effective VPN obfuscation breaks up these patterns so they look like normal browsing.
4. No Cert or Key Rotation
Stale certs or keys are gold for fingerprinting. If you run free or DIY stealth that reuses the same certs, one match lands you on a blocklist. A VPN with obfuscated servers rotates keys and certs daily to keep detection tools guessing.
5. Reused Exit IPs
Thousands sharing the same exit IP for weeks is a recipe for blacklists. Once flagged, all your users suffer. Serious VPN obfuscation relies on dynamic exit pools, with fresh IPs that avoid mass detection. Cheap “Free VPN obfuscation” setups skip this, and it shows.
Every single detection point above drives up support costs, refund rates, and churn. A smart stealth layer means fewer complaints and higher trust. If you run a VPN with obfuscated servers that shifts its shape constantly, you stay off blocklists longer and keep customers connected.
What Really Happens When You Skip Stealth?
When you don’t invest in real VPN obfuscation, you’re not just risking blocked connections — you’re building a business on a promise you can’t keep.
You Pay For Every Blocked Tunnel
When you don’t build VPN obfuscation into your white label service, you open a leak in your revenue stream.
One stale exit IP or default handshake gets fingerprinted — firewalls do their job. Entire user segments get cut off overnight.
When that happens, your brand’s promise of “secure, reliable access” breaks. Refunds come in. Support teams scramble. And your word-of-mouth growth stalls because you look like every other generic VPN that fails when it counts.
You Lose High-Value Customers Who Need Reliability
Some segments are especially sensitive:
- Enterprise clients: Remote teams behind corporate LANs that filter known VPN traffic.
- Expats and travelers: Users connecting from regions with smart DPI.
- Remote SaaS developers: Workers in places like the UAE or Turkey who depend on stealth to access Git repos and internal tools.
- ISPs and mobile carriers: Customers in regions where standard tunnels are throttled.
When these people can’t connect, they don’t complain quietly — they churn fast.
You Add Support Overhead You Didn’t Budget For
A tunnel that’s obvious is a tunnel that breaks. And every break means more work for your team.
Suddenly, your support desk deals with tickets like “Why can’t I connect from my office?” or “Why is my VPN dead on LTE?”
All because you skipped investing in a VPN with obfuscated servers that adapt as DPI rules change.
That’s money out the door in the form of extra headcount, longer resolution times, and customers you can’t save with apologies.
You Become the Brand That Failed When It Mattered
The big risk is reputation loss. In this space, trust is your only moat.
If your tunnel dies every time a country updates its blocklists, your resellers know it. So do your high-value customers.
A fragile “stealth mode” that’s static is worse than none at all. It’s false assurance that backfires.
How PureVPN’s Obfuscation Actually Keeps You Safe?
Live Stealth Health Status
312
Exit IPs Rotating Now
124
Port Changes (Last 24 hrs)
3
Fallback Protocols Live
Good stealth isn’t one switch. It’s a whole system that’s always changing to stay ahead of detection.
Here’s what a real VPN with obfuscated servers like PureVPN does behind the scenes so your users don’t get shut out.
TLS Wrapping
Your VPN traffic is wrapped inside regular HTTPS. That means when deep packet inspection tools look at it, they see what looks like normal encrypted web browsing. It’s the first and easiest way to avoid simple blocks. But it’s not enough by itself, which is why a proper obfuscation system keeps adding layers.
Header Morphing
Most cheap VPN setups fail because their handshake looks exactly the same every time. DPI tools catch that fast. PureVPN’s stealth mode changes the order and details in every handshake. This constant morphing makes fingerprinting far harder. It’s the kind of detail people miss when they try to duct-tape free VPN obfuscation scripts together.
Port Rotation
A static port like OpenVPN’s 1194 is basically a flag waving “I’m a VPN tunnel.” If you never rotate ports, firewalls can block you with one rule. PureVPN’s obfuscation changes ports automatically. It keeps your traffic unpredictable and much harder to shut down with a simple filter.
Pluggable Transports
Stealth isn’t foolproof. Firewalls get smarter. When they break through your main layer, you need a backup. PureVPN includes pluggable transports which can disguise VPN packets to look like normal HTTPS or harmless web requests. That fallback means your tunnel doesn’t collapse just because a new detection method shows up.
Exit IP Rotation
One of the most common mistakes in this space is sticking with the same exit IPs for too long. The longer an IP pool stays the same, the easier it is for blocklists to catch up. PureVPN’s stealth system rotates exit IPs constantly so you don’t get boxed in. This is what makes the PureVPN obfuscated servers list more reliable than half-baked free VPN obfuscation hacks.
It’s Managed — So You’re Not Fixing It Every Week
Every piece above is moving all the time — ports, certs, exit IPs, fallback modes. That’s the whole point. Obfuscation that doesn’t adapt will break. PureVPN keeps that rotation running for you, so you’re not hiring engineers just to patch stealth every time a country updates its blocklists. You sell uptime. We handle the layers that make that promise real.
How It Ties to Revenue, Not Just Privacy?
It’s easy to think of VPN obfuscation as just a technical feature. But for a serious VPN business, it’s more than that. Your tunnel is your product. If it stops working when users need it most — like when they’re on a restrictive network — you’re not just risking privacy complaints. You’re burning money every time someone clicks “Connect” and it fails.
Churn Leak Tester
Fewer Support Tickets
Every time your tunnel gets blocked because you don’t have proper obfuscation, your help desk has to deal with it. That means more time spent on issues you could have prevented. A robust obfuscation layer means fewer “Why can’t I connect?” tickets. For a lean team, that’s real overhead you keep off your books.
Lower Refund Rates
When a user pays for privacy and access, and you can’t deliver on the “access” part, the refund request is inevitable. This hits your cash flow and your reputation. A VPN with obfuscated servers that stays online in high-risk regions means your refund rate drops. That stability directly protects your monthly revenue.
Higher ARPU
Smart resellers know that stealth isn’t just a technical add-on — it’s an upsell. Many offer obfuscated VPN or “Stealth Mode” as a premium feature, branded as “censorship-resistant.” Users who need it are often the ones who pay more for reliable access. That means your average revenue per user (ARPU) can be significantly higher when your stealth layer actually works.
Less Churn
When you deliver a tunnel that stays up in tough regions, people stick around. They stop shopping for alternatives. If your VPN drops every time a new DPI rule shows up, they leave. Good obfuscation is retention insurance — it keeps users from switching to a competitor whose stealth setup actually holds up.
Reputation Word-of-Mouth
One thing that founders often overlook is that word-of-mouth about VPN reliability spreads fast. Look at any VPN obfuscation Reddit thread. Users talk about which brands work behind firewalls and which ones fail the second things get restrictive. That chatter makes or breaks you in regions where trust is everything. If your tunnel holds up, you’re the brand they recommend.
How We Handle It For You?
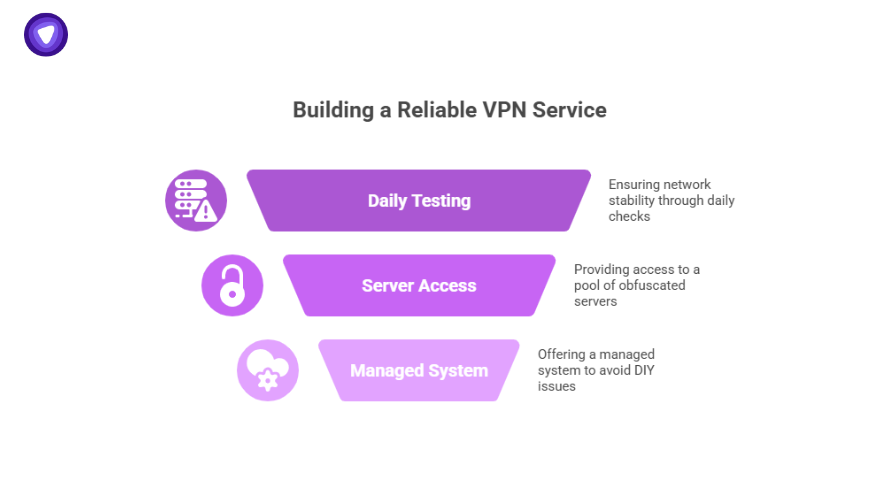
Running a white label VPN that holds up under real censorship pressure isn’t something you patch together overnight. PureVPN’s White Label gives you a tested stealth backbone that does the heavy lifting, so you’re not constantly chasing blocklists or patching fragile DIY setups.
Here’s what you get built in:
- Daily-Tested Stealth Network
Your tunnels plug into a system that’s checked and updated every day. No more surprises when a region updates DPI rules. - Full PureVPN Obfuscated Servers List
You’re not limited to a single stealth trick. You get access to a tested pool of obfuscated servers with multiple protocols, like OpenVPN stealth, and more. - No DIY Headaches
You’re not juggling half-baked free VPN obfuscation scripts. You get a managed system that adapts behind the scenes, so your uptime doesn’t depend on your team writing stealth patches at 2 a.m.
When you combine all this, you’re selling more than a tunnel. You’re giving your customers real-world reliability where others fail, and protecting your brand from the churn and refund mess that hits providers without proper stealth.
Stay Connected & Learn With Us
Join our growing community and connect with peers who build secure networks and resell privacy tools worldwide.
Performance Trade-Offs
If you’re promising stealth, you need to be upfront about the reality: VPN obfuscation isn’t magic that comes with zero impact. Adding extra layers to hide your tunnel’s signature means you’ll see some trade-offs. The key is designing it so your users get stealth only when they truly need it.
Performance Trade-Offs: Stealth On vs. Off
| Aspect | Performance |
|---|---|
| Speed | Normal |
| CPU Usage | Normal |
| Battery Impact | Normal |
It Costs a Bit More CPU and Latency
Every stealth layer — TLS wrapping, header morphing, fallback transports — takes extra processing. That means your tunnel’s speed will dip compared to a basic VPN connection running wide open. A good VPN with obfuscated servers handles this gracefully, but there’s no getting around physics. Your buyers should expect a slight bump in CPU usage on devices that run obfuscation all the time.
Extra Bandwidth Overhead
Techniques like padding packets or adding dummy traffic make it harder for DPI tools to fingerprint you by packet size. The trade-off is that you’re sending more data than you would with a normal VPN tunnel, which can mean slightly higher bandwidth costs.
Battery Drain on Mobile
Stealth layers can run constantly if your user is in a tough region. On mobile, that can hit battery life harder than a basic tunnel. This is why a good VPN with obfuscated servers should have efficient region toggles — so stealth runs only when needed.
Not Needed 24/7
Full-time obfuscation is overkill for many users. If your backbone has smart region-aware toggles, stealth only turns on when a user is in a country or network that inspects traffic heavily. This keeps the tunnel fast when it can be, and hidden when it must be.
Final Thoughts
Privacy means nothing if your tunnel fails the second someone needs it most. VPN obfuscation isn’t an extra feature — it’s your insurance that your product stays online when other services get blocked. Build on tested stealth. Keep your certs fresh. Rotate your exits. Adapt before blocklists do.
If you’re serious about selling a VPN that holds up in the real world — not just on paper — PureVPN White Label gives you the proven backbone to do it right.
Ready to keep your connections alive when it matters?


