White Label VPN App Integration is no longer a fringe idea. It is a deliberate strategy that enterprises, service providers, and tech platforms use to deliver a secure network access experience under their own brand.
In competitive digital environments where security and identity matter, integrating a white label VPN as a premium add‑on changes how companies position value and retain customers.
This blog explains the technical landscape of such an integration, the architectural requirements, deployment models, operational trade‑offs, and what success looks like when the integration is in production.
- White Label VPN Integration: Allows companies to embed VPN functionality under their own brand, providing a seamless, branded user experience.
- Premium Add-On: Offering it as a premium add-on creates a revenue opportunity while enhancing user security and privacy.
- Technical Components: Core components include authentication, VPN protocols, API integration, client software, and logging for operational visibility.
- Integration Approaches: Can be embedded via SDKs or hosted as a service, with trade-offs in control, maintenance, and scalability.
- Security and UX: Must prioritize encryption, kill switches, DNS protection, multi-platform support, and monitoring for performance and user experience.
What White Label VPN App Integration Really Means
The term White Label VPN App Integration refers to embedding or bundling virtual private network functionality into an existing application or service under a client’s brand. This is not a generic rebrand of a third‑party consumer VPN application on an app store. It means embedding core VPN functions into a service stack so users never feel they are leaving the brand’s ecosystem.
A true integration combines authentication, network tunneling, policy enforcement, logging, and support. The goal is to deliver secure access, privacy, and traffic routing while preserving a consistent brand experience.
Why Enterprises Choose a Premium Add‑On Model
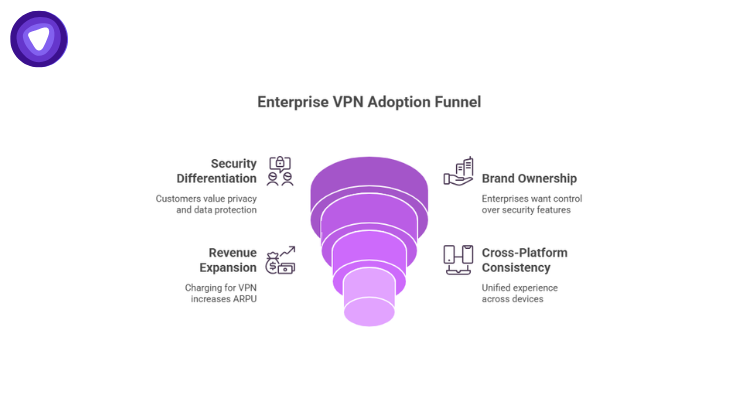
Adding VPN capabilities as a premium add‑on makes sense when:
- Security is a differentiator
Customers care about privacy and data protection. A secure network connection assures users that their data is not exposed on untrusted networks. - Brand ownership matters
Enterprises want full control over how security features appear and behave. White label VPN integration removes dependencies on external branded clients. - Revenue expansion is strategic
Charging for a premium network protection layer can increase ARPU (average revenue per user) without building the entire stack from scratch. - Cross‑platform consistency is required
Whether the client is on a mobile app, desktop application, or embedded device, the premium add‑on offers a unified experience.
Core Technical Components of White Label VPN App Integration
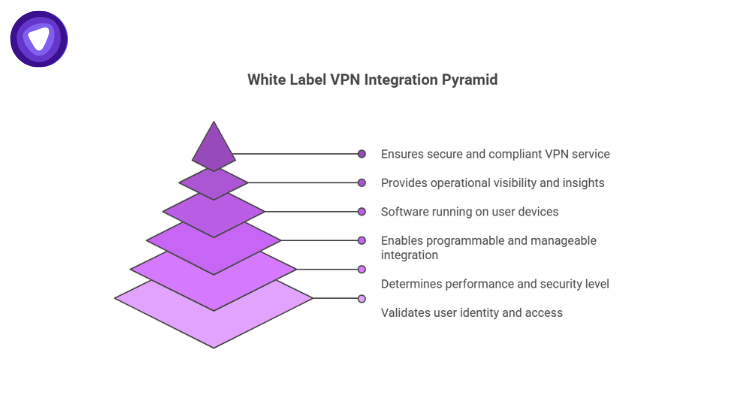
Technical clarity ensures that decisions around integration are systematic and scalable. Below are core components any engineering team should evaluate.
1. Authentication and Access Control
Before a user accesses the VPN service, their identity must be validated. Typically this involves:
- Token‑based authentication linked to the primary application’s user database
- OAuth2 or similar standards for session management
- Role‑based access control to define who can use the premium add‑on
Authentication ties the VPN service to enterprise user accounts.
2. VPN Protocol Stack
Deciding which underlying VPN protocol to support impacts performance, compatibility, and security. Common protocols include:
| Protocol | Security Level | Performance | Use Cases |
| OpenVPN | High | Medium | All‑purpose |
| WireGuard | High | High | Mobile / modern endpoints |
| IKEv2 | Medium‑High | High | Mobile reliability |
Choosing the protocol aligns with user expectations and device support requirements.
3. API Integration Layers
API endpoints make the integration programmable and manageable:
- Session initiation APIs start and manage VPN tunnels
- Policy APIs define network rules and access rights
- Telemetry APIs collect usage metrics and health data
APIs must be secure, authenticated, and versioned to support ongoing operations.
4. Endpoint Clients
This refers to the software running on user devices. For white label integration:
- Custom UI shells wrap core VPN functions
- Configuration provisioning is automated via APIs
- Clients handle key management and reconnect logic
Developers can either embed SDKs or integrate with lower‑level network drivers depending on platform capabilities.
5. Logging and Analytics
Operational visibility is critical:
- Connection success rates
- Data usage patterns
- Latency and throughput metrics
- Gateway performance
Logs are essential for troubleshooting and understanding how customers use the premium add‑on.
6. Security Policies and Compliance
A secure integration needs well‑defined policies:
- Kill switch enforcement
- DNS leak protection
- Encryption standards
- Endpoint compliance checks
These policies ensure the VPN service does what users and administrators expect.
Integration Approaches: Embedded vs Hosted Components
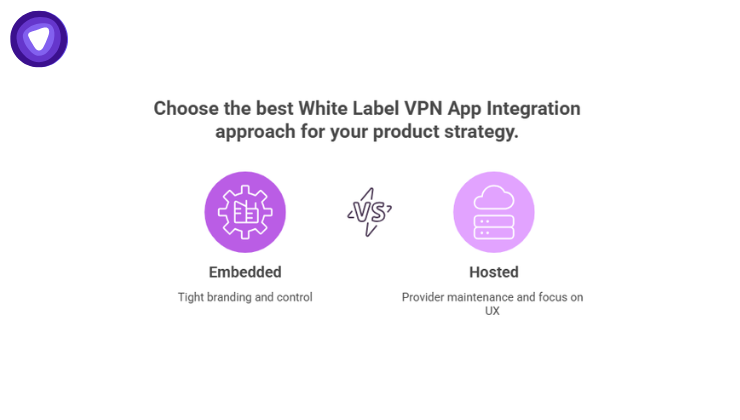
White Label VPN App Integration can be implemented using different architectural models depending on how much control a product team wants over infrastructure, development, and long term maintenance.
Embedded (SDK‑Driven)
In this model the VPN logic is embedded directly into the host application. It offers:
- Tight branding control
- Faster launch of features within the app experience
- Direct control over updates
Trade‑offs include:
- Larger initial development effort
- Maintaining SDK compatibility across platforms
Hosted (Service‑Oriented)
Here, the VPN infrastructure runs externally and the host app merely triggers sessions and UI flows:
- Infrastructure is maintained by a provider
- The enterprise focuses on user experience
Trade‑offs include:
- Potential lag in feature parity
- Dependency on vendor APIs and SLAs
Both approaches serve different product strategies. Labs often compare time to market, internal expertise, and long‑term maintenance costs before choosing.
Performance, Scalability, and Capacity Planning
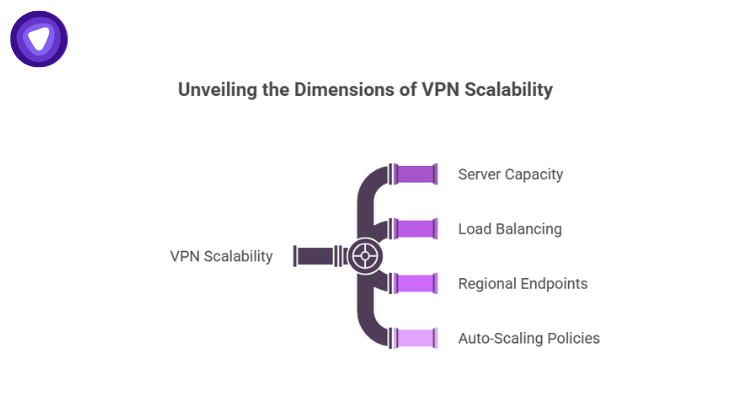
A properly integrated white label VPN must scale efficiently. Key considerations include:
- Server capacity to handle peak concurrent sessions
- Load balancing across gateways
- Regional endpoint provisioning to reduce latency
- Auto‑scaling policies to address demand spikes
It is common to architect VPN services as distributed clusters capable of horizontal scaling. Stats from recent infrastructure studies show that dynamic scaling can reduce network congestion by up to 35 percent under load when properly configured.
Peak performance also ensures that premium users do not see degraded throughput during high traffic periods.
User Experience Considerations
When embedding VPN functionality into an app, user experience plays an important role in adoption and usability. The interface should clearly label premium network protection features so users understand the value of the service. Simple toggle controls for connecting and disconnecting make the VPN easy to use without requiring technical knowledge.
Readouts that display connection status and gateway region help users verify that the service is active and functioning properly. Error messages should explain connection issues in plain language rather than technical jargon so users can resolve problems quickly. A well designed user experience reduces support requests and encourages consistent usage.
Security Risks and Mitigations
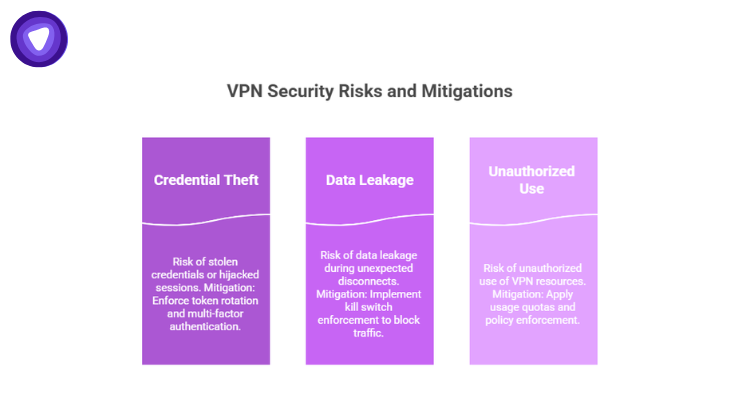
Any network service carries risk. For a white label VPN:
Risk: Credential theft or session hijacking
Mitigation: Enforce token rotation and multi-factor authentication.
Risk: Data leakage during unexpected disconnects
Mitigation: Implement kill switch enforcement to block traffic if the VPN connection drops.
Risk: Unauthorized use of VPN resources
Mitigation: Apply usage quotas and policy enforcement to control access and bandwidth consumption.
Security should be integrated across every layer of the architecture, including API gateways, authentication systems, and client network stacks.
Monitoring, Support, and SLA Requirements
Operational teams require reliable monitoring and support capabilities to maintain service performance. This includes real time alerts that track service health, automated recovery workflows that restore connectivity during disruptions, and monitoring systems that ensure SLA adherence.
When VPN functionality is offered as a premium add on, support expectations increase. Enterprises should therefore establish dedicated support channels and clear documentation specifically related to the VPN service so users can resolve issues quickly and maintain confidence in the platform.
Commercial and Licensing Models
Introducing White Label VPN App Integration as a premium add on also creates new monetization opportunities for businesses. Many companies implement subscription tiers that include VPN access as part of higher service plans.
Others adopt usage based billing models where pricing is tied to data consumption or bandwidth usage. Enterprise focused offerings often rely on licensing structures with per seat fees for organizations deploying VPN access across teams.
Licensing strategies should align with infrastructure capacity planning so that service providers avoid under provisioning resources or facing unexpected operational costs as adoption grows.
Case Study Summary Table
The following table summarizes typical architectural choices enterprises make when integrating a white label VPN solution.
| Dimension | Option A | Option B | Impact |
| Integration Style | Embedded SDK | Hosted Service | Embedded gives UI control; hosted reduces maintenance |
| Protocol Choice | WireGuard | OpenVPN | WireGuard improves performance; OpenVPN broad compatibility |
| Authentication | Token‑Based | OAuth2 | Both are secure; OAuth2 eases federation |
| Scalability | Auto‑Scaling | Fixed Cluster | Auto‑scaling adjusts to demand; fixed is predictable cost |
| Logging | Local + Central | Central Only | Local logs aid debugging; central logs for analytics |
This table supports technical decision making based on the enterprise’s priorities.
Implementation Roadmap
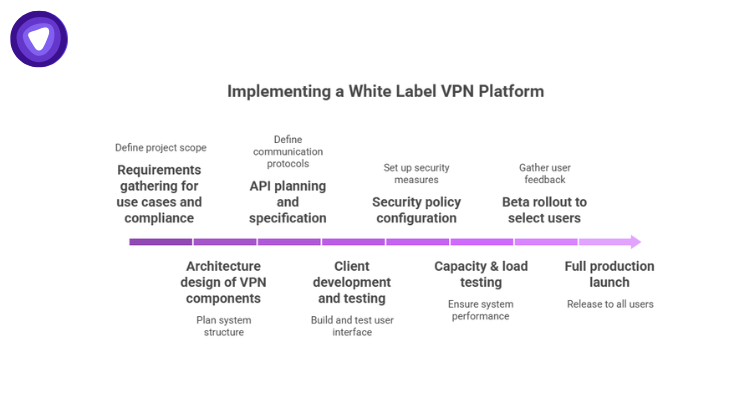
A concise roadmap helps engineering and product teams coordinate:
- Requirements gathering for use cases and compliance
- Architecture design of VPN components
- API planning and specification
- Client development and testing
- Security policy configuration
- Capacity & load testing
- Beta rollout to select users
- Full production launch
Each phase needs checkpoints and success criteria. A phased rollout reduces risk and aligns expectations across teams.
Integration Challenges and Solutions
Many integrations encounter common challenges that must be addressed for successful deployment. Cross-platform client disparities can create inconsistencies in performance and behavior, so it is important to abstract network logic into reusable modules that work across devices.
Maintaining high performance while encrypting traffic is another key challenge, which can be addressed by optimizing VPN gateways and selecting efficient protocols.
In-house teams often face a learning curve when managing integration, making clear documentation, training, and support from third-party partners essential. Overall, success requires both tactical planning and disciplined operational management.
How White Label VPN App Integration Benefits Users
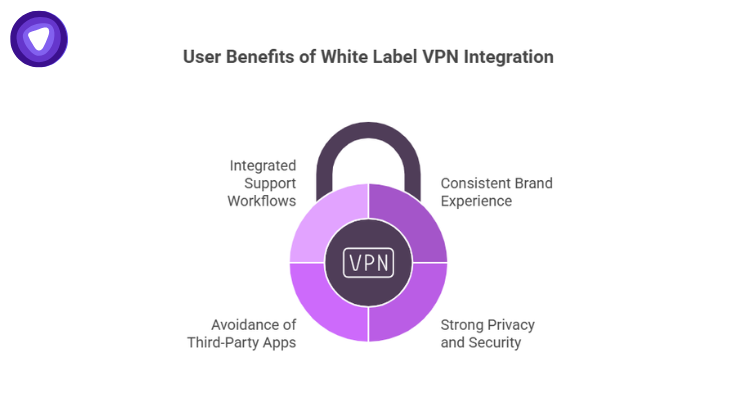
These benefits increase trust and retention.
When users engage with a premium add‑on built on a solid white label VPN integration:
- They enjoy consistent brand experience
- They get strong privacy and secure access
- They avoid third‑party branded apps
- They experience integrated support workflows
These benefits increase trust and retention.
Where PureVPN’s White Label VPN Solution Fits
For organizations ready to deploy White Label VPN App Integration as a premium add‑on, a solution built for enterprise contexts is essential. PureVPN’s white label VPN solution supports API‑driven integration, multiple protocol options, automated provisioning, and analytics. It aligns with strict authentication flows and policy controls that large platforms require.
This solution is engineered to operate at scale and to integrate with existing user identity systems. It enables companies to offer secure network access directly within their product experience with consistent performance across regions.
From authentication to telemetry, the infrastructure supports the technical components outlined in this discussion.
Final Thoughts
White Label VPN App Integration is a strategic investment for companies that want to provide secure network access while maintaining brand continuity. It demands clear architecture, thoughtful protocol selection, meticulous security policies, robust logging and analytics, and a premium user experience. When implemented with discipline, such an integration adds measurable value to a product suite and deepens user engagement.
Using White Label VPN App Integration as a premium add‑on helps enterprises differentiate their offerings, support secure user behavior, and expand revenue with a technically sound, user‑focused network security feature.


