- VPN protocols determine speed, security, stability, and overall user experience in white label VPN platforms.
- OpenVPN offers broad compatibility and reliability, making it ideal for desktops and cross-platform support.
- WireGuard provides the fastest connections, low latency, and efficient performance for both desktop and mobile users.
- IKEv2 excels in mobile environments, reconnecting quickly when switching between networks, while IPsec suits enterprise and site-to-site deployments.
- Protocol selection impacts infrastructure load, encryption strength, and scalability, making it a critical business and technical decision for white label VPN operators.
A VPN does not fail because of weak encryption. It fails because the wrong user gets access.
In a white label VPN business, authentication is the control layer that determines who can connect, how access is verified, and how sessions are managed across thousands of users. If identity checks are weak, encryption becomes irrelevant.
This blog explains how user authentication works in white label VPN services and how the architecture supports secure, scalable deployments.
What Is User Authentication?
User authentication is the process of verifying that a person or system attempting to access a service is who they claim to be. It typically relies on one or more identity factors:
- Something the user knows, such as a password
- Something the user has, such as a one time code or device
- Something the user is, such as biometric verification
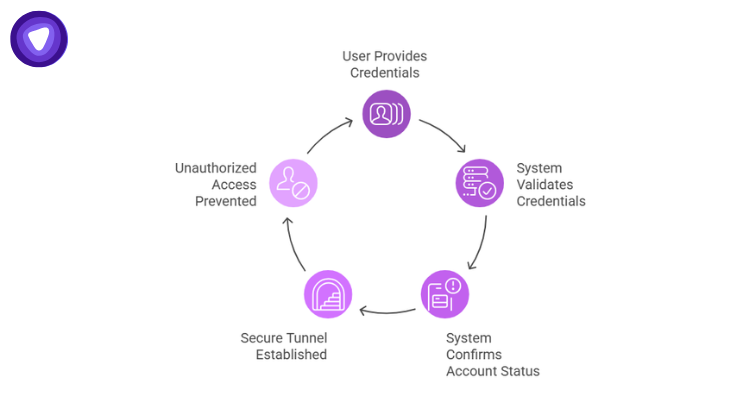
In VPN services, authentication happens before a secure tunnel is established. The system validates credentials, confirms account status, and only then allows the connection request to proceed. Without this verification layer, encrypted traffic could still originate from unauthorized users.
Why Authentication Is Central to VPN Security
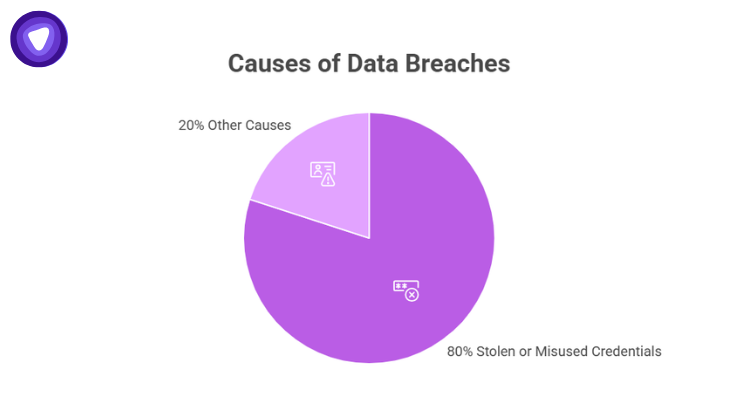
Credential abuse remains one of the most common breach vectors.
- A report found that over 80 percent of breaches involve stolen or misused credentials.
- IBM’s 2024 Cost of a Data Breach Report shows the global average breach cost reached 4.45 million USD in 2023.
- Microsoft reported in 2023 that it blocks more than 7,000 password attacks per second.
- A report confirms continued growth in multi factor authentication adoption across enterprises.
For VPN providers, weak authentication increases account takeover risk, infrastructure abuse, and customer churn. White label VPN services must therefore embed secure identity validation into the service architecture.
The Core Authentication Flow in White Label VPN Services
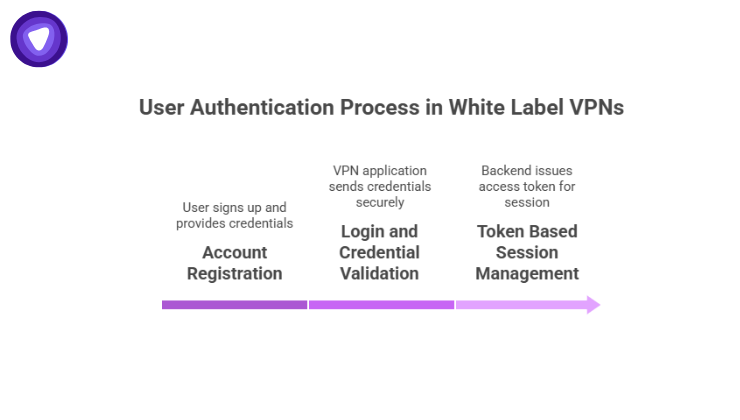
User authentication in a white label VPN environment typically follows a structured sequence.
1. Account Registration
When a user signs up:
- Credentials such as email and password are collected.
- Passwords are securely hashed before storage.
- Verification steps such as email confirmation may be triggered.
This establishes the identity record inside the VPN provider’s backend system.
2. Login and Credential Validation
When a user logs in:
- The VPN application sends credentials securely over TLS.
- The backend validates the submitted password against the stored hash.
- If validated, the system generates a session context for the user.
In modern deployments, repeated password validation is avoided by issuing short lived authentication tokens.
3. Token Based Session Management
Token based authentication reduces exposure of raw credentials.
- After successful login, the backend issues an access token.
- The VPN client uses this token to request server information and initiate a VPN session.
- Expired or invalid tokens prevent tunnel establishment.
This design isolates identity verification from VPN traffic handling.
Authentication Methods Commonly Used
White label VPN services support different authentication models depending on the business model and target market.
| Authentication Model | Description | Typical Deployment |
| Username and Password | Standard credential validation against internal database | Consumer VPN apps |
| Token Based Authentication | Access token issued after login to authorize sessions | API driven VPN platforms |
| API Authentication | Platform authenticates with backend using secret keys to retrieve access tokens | White label integrations |
| Single Sign On Integration | External identity provider manages user login | Enterprise deployments |
The authentication model must align with how the VPN brand manages users and distributes access.
Backend Architecture Behind Authentication
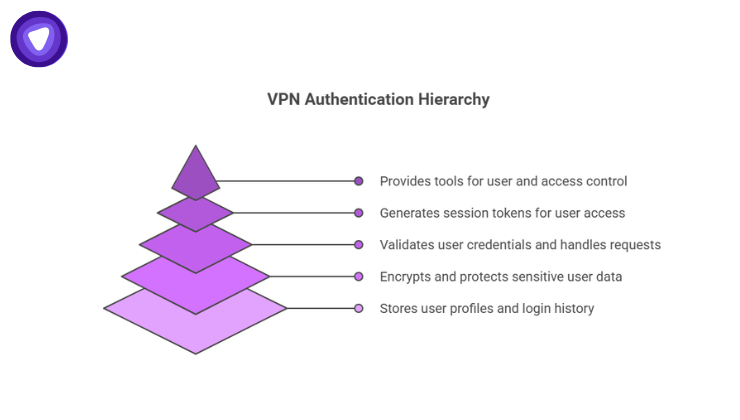
In white label VPN services, the authentication system operates independently from VPN server infrastructure. This ensures that user identities are verified before any VPN tunnel is created, reducing the risk of unauthorized access.
Core Components
- Authentication API Layer: Handles incoming requests from apps or client software and validates credentials.
- Secure Credential Storage: Stores passwords, keys, and tokens in an encrypted, tamper-proof manner.
- Access Token Issuance System: Generates session tokens that control the duration and scope of user access.
- User Account Database: Maintains user profiles, device limits, and login history.
- Admin Management Interface: Provides centralized tools for user management, access control, and reporting.
Benefits of Separation
- Identity Validation First: Ensures users are authenticated before VPN connections are established.
- Centralized Session Control: Administrators can revoke sessions in real time, enhancing security.
- Traceable API Interactions: Every authentication call is logged and monitored for audit and compliance purposes.
The authentication layer effectively acts as a gatekeeper between users and network resources, making it a critical component in maintaining security, usability, and scalability for white label VPN services.
Authentication and Access Control
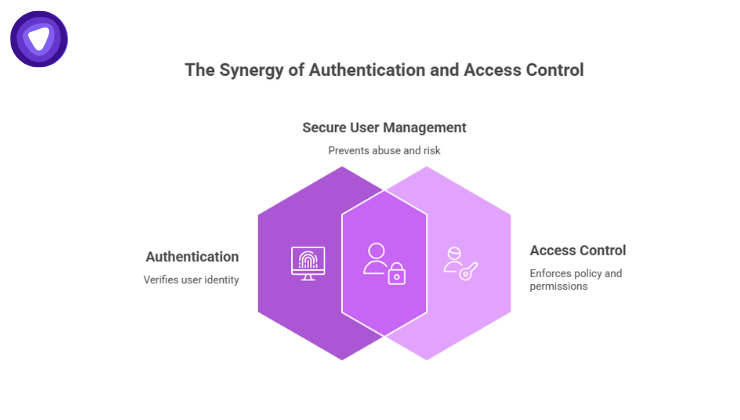
Authentication confirms identity. Authorization enforces policy. White label VPN platforms commonly implement:
- Active subscription validation before connection
- Account suspension controls
- Centralized user lifecycle management
- API driven onboarding and deprovisioning
Secure authentication reduces account abuse, infrastructure misuse, and operational risk.
Why Authentication Defines Long Term Viability
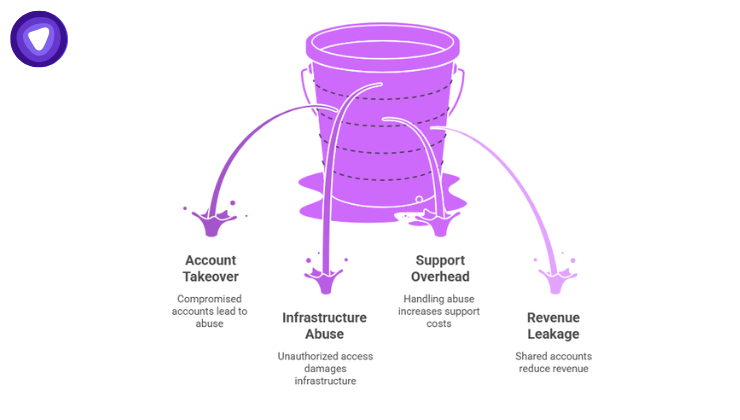
A white label VPN business scales on user volume. As volume grows, identity risks grow with it. Secure authentication reduces:
- Account takeover incidents
- Infrastructure abuse
- Support overhead
- Revenue leakage from shared or compromised accounts
Encryption protects data in transit. Authentication protects the service itself. For any white label VPN provider, identity architecture is core infrastructure, not an optional feature.
Authentication in PureVPN White Label VPN Solution
PureVPN White Label VPN Solution provides a secure backend for managing user access via API and SDK integration. Branded VPN applications authenticate users by connecting to this backend, which issues access tokens and manages session workflows. This system handles login verification, session establishment, and centralized user account management through the partner dashboard, giving full control over your branded app’s users.
Partners can also leverage the admin console and API vault to configure users, servers, and access policies, while automating account provisioning and billing.
PureVPN handles the underlying infrastructure, including secure credential storage and session validation, so VPN brands can offer seamless authentication and connection experiences without building their own identity systems.
Final Thoughts
User authentication defines the security posture of any white label VPN service. Encryption protects data in transit. Authentication protects the network itself. Providers that treat identity management as core infrastructure build stronger, more sustainable VPN businesses.


