- White Label VPN Procurement: White Label VPN Procurement must be treated as a compliance-first decision because the VPN becomes part of your product’s security and data processing chain, not just a third-party tool.
- Regulatory Compliance: Regulatory frameworks like GDPR, SOC 2, ISO 27001, and regional data sovereignty laws directly define how VPN data is collected, stored, and transmitted, making them central to procurement decisions.
- Security Controls: Encryption alone is not sufficient for compliance. Logging policies, auditability, identity management, and multi-tenant isolation determine whether a VPN is truly enterprise-ready.
- Infrastructure & Jurisdiction: Infrastructure transparency and jurisdiction control are critical because hidden server dependencies or unclear data locations can create legal exposure and operational risk.
- Vendor Accountability: Vendor due diligence and continuous operational control are essential since weaknesses in the VPN provider’s security model directly become risks for every client using the white label service.
A VPN can quietly become the weakest control in your infrastructure if procurement is treated as a feature comparison exercise. Encryption strength and server count look sufficient on paper, yet the real exposure sits in logging policies, jurisdictional reach, and access control gaps that only surface under audit or incident review. This is where White Label VPN Procurement shifts from a technical purchase to a compliance-critical decision, especially when the VPN is embedded into a broader service or product.
Once the VPN operates under your brand, responsibility does not stay with the provider. It extends to how data is processed, routed, and stored across every user environment. That shift makes compliance the defining factor, not performance alone, because the service effectively becomes part of your own security architecture.
Why Regulatory Compliance Is Non-Negotiable
Regulatory compliance defines how data moves through your system, not just how it is protected. When a VPN is integrated into your product, it becomes part of your data processing chain. That means any misalignment with global standards directly affects your legal exposure and customer trust. This is why White Label VPN Procurement must be evaluated against established regulatory frameworks from the outset.
Key Regulations That Shape VPN Requirements
These regulations define the minimum legal and operational standards a VPN must meet to ensure data is processed, stored, and transmitted in a way that aligns with global privacy and security expectations.
GDPR (General Data Protection Regulation)
Applies to any organization handling EU user data.
Relevant VPN implications:
- IP addresses and session logs qualify as personal data
- Strict controls on cross-border data transfers
- Mandatory auditability and user data access rights
If the VPN logs user metadata without clear control or stores it in unrestricted jurisdictions, the entire service risks non-compliance even if encryption remains strong. In a white label environment, this exposure extends to every client using the service.
Read more on GDPR for SaaS providers here.
SOC 2 (Service Organization Control Type II)
Focuses on how service providers manage data securely.
Key VPN considerations:
- Infrastructure security and uptime reliability
- Monitoring and incident response
- Controlled access to sensitive systems
SOC 2 alignment ensures that the VPN operates within enforceable security controls rather than undocumented practices, which becomes essential when the service is delivered under another brand.
ISO/IEC 27001
Defines how information security is managed systematically.
Relevant controls include:
- Risk assessment frameworks
- Access management policies
- Cryptographic enforcement
- Continuous monitoring
A VPN without structured risk controls introduces unpredictability into your broader security posture, particularly when deployed across multiple client environments.
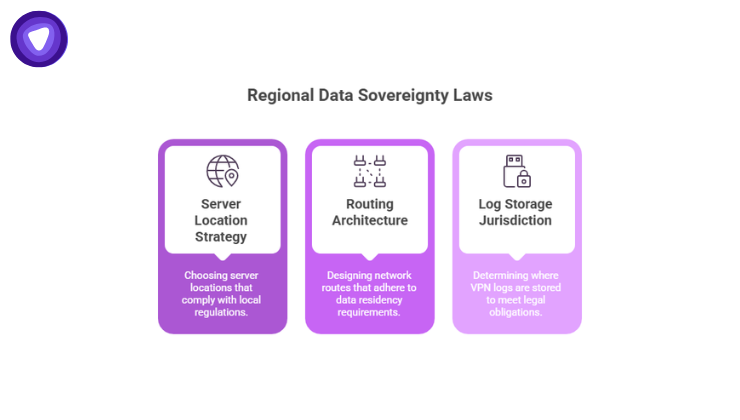
Regional Data Sovereignty Laws
Different countries enforce rules on where data must reside and how it is processed.
Impact on VPN procurement:
- Server location strategy
- Routing architecture
- Log storage jurisdiction
In White Label VPN Procurement, this becomes more complex because different clients may operate under different regulatory environments simultaneously.
The Real Reason Compliance Matters
Compliance failures rarely begin as regulatory violations. They originate in design decisions such as logging too much data, routing traffic through non-compliant regions, or failing to isolate users properly.
According to the IBM Cost of a Data Breach Report, the average breach cost reached $4.88 million, and organizations with strong compliance automation reduced costs by over $1.7 million. This establishes compliance as a financial control, not just a legal requirement.
For White Label VPN Procurement, the impact multiplies. The VPN is not protecting a single organization. It is supporting multiple environments under one service layer, where any gap becomes a shared risk across all users.
Core Compliance Domains to Evaluate
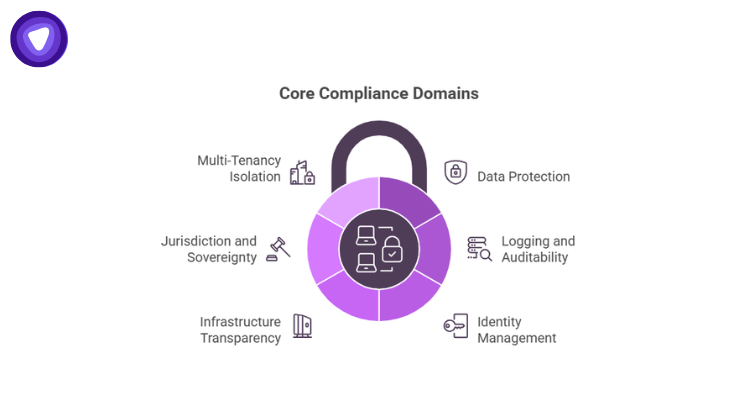
Each domain below defines a critical control layer that determines whether the VPN can operate as a compliant component within a larger service environment.
- Data Protection and Encryption Standards
Strong encryption is foundational, but compliance requires consistency and enforceability.
Key checks:
- AES-256 encryption across all tunnels
- Secure protocols such as WireGuard or OpenVPN
- Forward secrecy implementation
- DNS leak protection and secure resolution
Encryption must be uniformly applied across all tenant environments. Any variation creates uneven exposure, which is unacceptable when the VPN operates as part of a distributed service.
- Logging, Auditability, and Data Retention
The absence of logs does not equal compliance. Enterprises require controlled visibility.
Evaluation points:
- Type of metadata collected (IP, timestamps, session data)
- Storage location and jurisdiction
- Retention duration and deletion mechanisms
- Accessibility for audits and investigations
An IBM Security study found that 68% of breaches involve human factors, including credential misuse. Without audit logs, identifying misuse becomes nearly impossible. In a white label model, logging must balance privacy with traceability across all client environments.
- Identity and Access Management Integration
VPN access must align with existing identity systems rather than operate independently.
Requirements include:
- SSO integration using SAML or OAuth
- Multi-factor authentication enforcement
- Role-based access control
This ensures consistent access governance across the organization. In White Label VPN Procurement, these controls must scale across multiple tenants without requiring manual configuration for each environment.
- Infrastructure Transparency and Server Control
Opaque infrastructure introduces compliance blind spots.
Key considerations:
- Dedicated vs shared servers
- Physical vs virtual infrastructure
- Ownership and third-party dependencies
- Visibility into server locations
Dedicated infrastructure reduces cross-tenant exposure and ensures predictable performance. This is critical when the VPN underpins a service offered to external clients.
- Jurisdiction and Data Sovereignty
Legal exposure depends on where data is processed and stored.
Checklist:
- Country of provider incorporation
- Data retention laws in server regions
- Exposure to government access requests
- Cross-border transfer safeguards
For White Label VPN Procurement, jurisdictional misalignment can restrict market access or create compliance conflicts across regions.
- Multi-Tenancy and Isolation Controls
Multi-tenant environments require strict separation between users.
Critical controls:
- Network segmentation
- Isolated authentication layers
- Separate IP pools
- Independent configuration environments
Without proper isolation, one compromised environment can affect others. This risk increases significantly when the VPN is deployed across multiple client-facing environments.
Compliance Checklist
Each of these controls becomes more critical in White Label VPN Procurement because the VPN functions as part of a larger distributed service rather than a standalone tool.
| Compliance Area | Key Requirement | Risk if Ignored |
| Encryption | AES-256, secure tunneling protocols | Data interception |
| Logging & Auditability | Controlled logs with audit access | No incident traceability |
| Identity Integration | SSO, MFA, RBAC | Unauthorized access |
| Infrastructure Transparency | Dedicated, visible server architecture | Hidden vulnerabilities |
| Jurisdiction Control | Region-specific compliance alignment | Legal and regulatory exposure |
| Multi-Tenancy Isolation | Segmentation and tenant separation | Cross-tenant data leakage |
| IP Management | Dedicated IP allocation | Shared reputation and access risk |
Performance and Compliance Are Interconnected
Performance shortcuts often introduce compliance risks. Shared infrastructure, overloaded nodes, and weak routing policies may reduce cost but increase exposure.
A report found that over 60% of organizations experienced security incidents linked to remote access tools, often due to misconfiguration and lack of visibility. That reinforces the need for infrastructure that supports both performance and compliance simultaneously.
In a white label setup, performance consistency must be maintained across all tenants, since any degradation directly impacts service reliability and trust.
Dedicated IP and Access Control Requirements

Shared IP environments create unpredictable risk. Activity from one user can affect the entire IP range.
Dedicated IP allocation ensures:
- Clean reputation management
- Stable access to platforms and services
- Clear attribution of user activity
In White Label VPN Procurement, dedicated IPs allow each client environment to operate independently, preventing risk spillover across tenants.
Vendor Due Diligence Beyond Surface Claims
Procurement decisions must go beyond marketing claims.
Verification should include:
- SOC 2 or ISO 27001 certifications
- Independent audit reports
- Penetration testing results
- Documented incident response processes
A 2025 industry report indicates that over 55% of enterprises consider switching vendors after a security incident, even if impact is limited. Vendor reliability directly affects customer retention when the VPN is part of your offering.
Operational Control and Management Layer
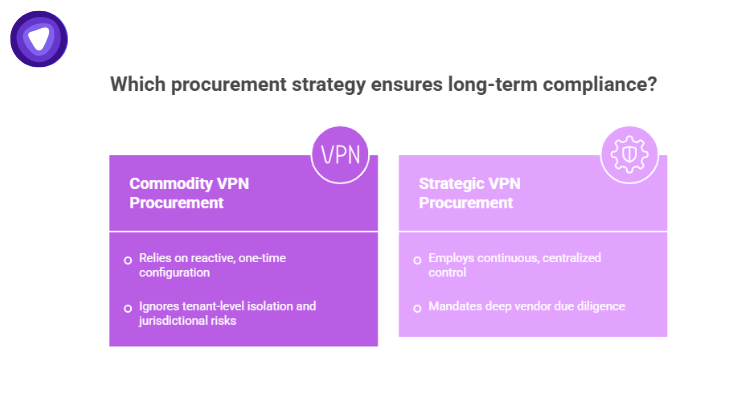
Compliance requires continuous control, not one-time configuration.
Essential capabilities:
- Centralized user management
- Policy enforcement across teams
- Usage monitoring and reporting
- Real-time access adjustments
Without a strong management layer, compliance becomes reactive. In White Label VPN Procurement, this layer must scale across multiple environments without increasing operational complexity.
Where Procurement Processes Fail
Common gaps include:
- Treating VPNs as commodity tools
- Ignoring tenant-level isolation
- Overlooking jurisdictional implications
- Accepting logging claims without verification
These issues rarely appear during onboarding. They surface during audits, incidents, or customer escalations, when remediation becomes costly and disruptive.
Practical Alignment with Business Use Cases
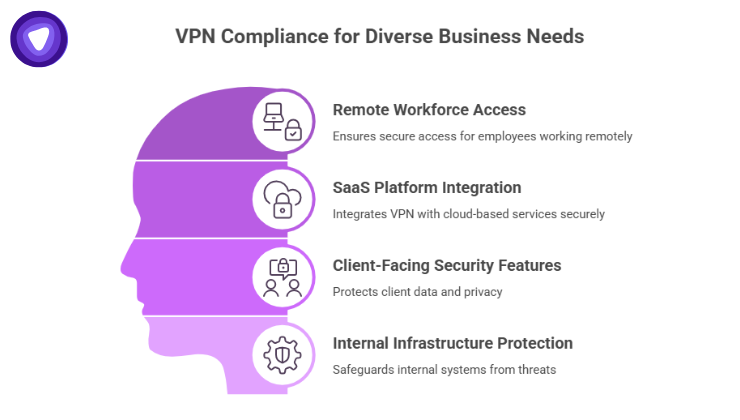
A compliant VPN must support multiple operational scenarios:
- Remote workforce access
- SaaS platform integration
- Client-facing security features
- Internal infrastructure protection
Each use case introduces different compliance requirements. In White Label VPN procurement, the challenge is maintaining consistent controls across all of them without introducing gaps.
Where PureVPN White Label VPN Solution Fits
PureVPN’s white label VPN solution aligns with these compliance requirements by offering dedicated infrastructure options, controlled logging configurations, and flexible identity integrations. This allows businesses to maintain consistent data protection and access control standards across all user environments without introducing fragmentation.
Its architecture supports tenant isolation, dedicated IP allocation, and centralized management, enabling organizations to deliver VPN functionality as part of their service while retaining full visibility and operational control over compliance requirements.
Final Thoughts
Compliance is the factor that determines whether a VPN strengthens your security posture or introduces hidden risk. White Label VPN Procurement extends this responsibility across multiple environments, where encryption, logging, identity control, and jurisdiction must work together as a unified system.
When procurement is guided by compliance requirements rather than surface-level features, the VPN becomes a controlled and scalable component of your infrastructure. Without that foundation, it remains an unmanaged layer that exposes both your business and your customers to avoidable risk.


