- Embedded VPNs: Move privacy from a user-controlled action to a built-in application function that runs automatically.
- Standalone VPN Limits: Require manual activation, which creates security gaps and inconsistent protection across sessions and devices.
- Modern Platforms: SaaS, fintech, and super apps need continuous, system-level encryption instead of session-based VPN use.
- Embedded Privacy Model: Improves consistency through encrypted tunnels, identity-based access, and automatic routing at the platform level.
- White Label VPN: Enables businesses to embed VPN infrastructure into their products without building complex backend systems.
Privacy used to depend on users manually connecting to a VPN. That creates gaps. Traffic outside active sessions stays unprotected, and there is no enforcement across apps, APIs, or background processes.
For SaaS platforms, fintech apps, and distributed teams, this model does not hold. Data moves continuously, not in sessions.
That is why VPN functionality is shifting into the application layer. Secure tunnels are established by default, traffic is routed through controlled infrastructure, and access is tied to identity, not user action.
The Problem with Standalone VPN Apps
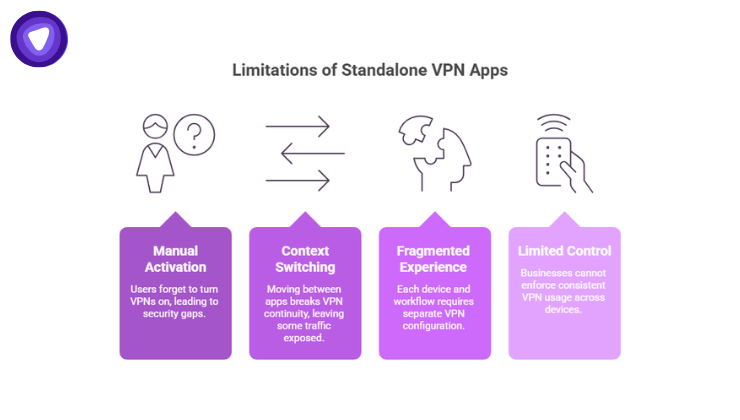
Standalone VPNs solved an early problem: securing traffic over public networks. But their design assumes user discipline. That assumption fails in real-world usage.
Key limitations:
- Manual activation: Users forget to turn VPNs on. Even security-aware users miss sessions.
- Context switching: Moving between apps breaks continuity. A secure connection in one app does not extend to others.
- Fragmented experience: Each device, browser, or workflow requires separate configuration.
- Limited control for platforms: Businesses cannot enforce consistent usage across customers or employees.
The result is predictable. Security gaps appear not because the technology fails, but because it depends on user behavior.
A report by IBM Security found that 68% of breaches involve human factors, including misconfigurations and inconsistent usage. Standalone VPNs fall directly into this gap.
The Rise of Embedded Privacy
Embedded privacy shifts security from a user action to a built-in system function. Instead of asking users to enable protection, applications integrate secure networking directly into their architecture, ensuring consistent protection across all sessions.
This includes in-app encrypted tunnels, automatic routing through secure gateways, identity-based access controls, and region-based traffic handling without user input.
In practice, a banking app encrypts all traffic by default, a SaaS platform routes team access through private networks, and a content platform manages geo-access internally. Users do not activate privacy; it remains continuously enforced.
This model aligns with modern system design where security is always active, invisible to the user, and enforced at the platform level.
Why Embedded VPN Is Winning
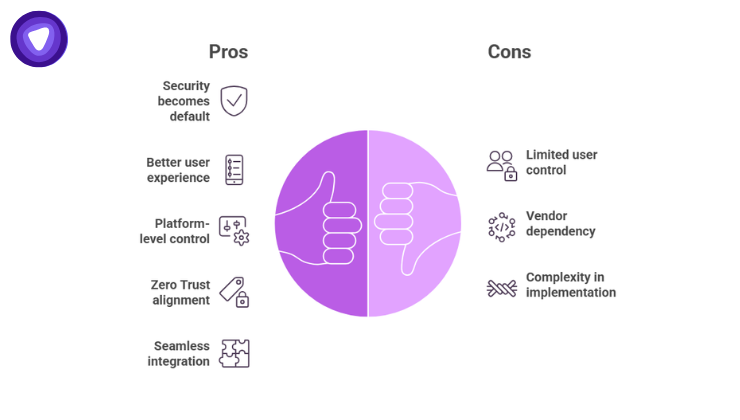
Security requirements are shifting toward continuous enforcement within application environments, where protection is applied at the system level rather than depending on user-driven tools or external connections.
1. Security Becomes Default, Not Optional
When VPN functionality is embedded, there is no “off” state.
- No reliance on user behavior
- No gaps between sessions
- No exposure during app switching
This closes one of the most common breach pathways: unsecured sessions due to human oversight.
Human error remains a dominant factor in security incidents, reinforcing the need for systems that reduce user dependency.
2. Better User Experience Without Tradeoffs
Standalone VPNs introduce friction:
- Slower speeds due to generic routing
- App switching
- Login interruptions
Embedded VPNs remove these barriers by integrating directly with application logic.
- Traffic routing is optimized per use case
- Authentication aligns with app sessions
- Performance is tuned for specific workloads
Users experience security without noticing it.
3. Platform-Level Control for Businesses
For companies, embedded VPNs provide something standalone apps cannot: control.
With embedded VPN:
- Access policies are enforced centrally
- Traffic flows are defined by the platform
- Logs and monitoring are unified
With standalone VPN:
- Users control activation
- Visibility is limited
- Enforcement is inconsistent
This distinction matters for SaaS providers, fintech platforms, and remote-first companies that manage distributed users.
4. Alignment with Zero Trust Architecture
Modern security frameworks follow zero trust principles:
- Verify every request
- Limit access based on identity
- Assume no network is inherently secure
Embedded VPNs fit naturally into this model.
Instead of granting broad network access, they:
- Create app-specific secure tunnels
- Restrict access to defined resources
- Integrate with identity systems
Standalone VPNs, by contrast, often grant full network access once connected.
5. Seamless Integration with Modern Apps
Applications today handle:
- Payments
- Messaging
- File sharing
- Identity verification
All within a single interface.
This convergence requires security that moves with data, not separate tools that sit outside the workflow.
A 2025 industry analysis by Gartner indicates that over 70% of new digital platforms will embed security controls directly into application layers, reducing reliance on external tools.
Standalone VPN vs Embedded VPN: A Clear Comparison
This shift is structural, not incremental. It reflects how software is built today.
| Aspect | Standalone VPN Apps | Embedded VPN |
| Activation | Manual | Automatic |
| User dependency | High | Minimal |
| Security coverage | Session-based | Continuous |
| Integration | External tool | Native feature |
| Performance optimization | Generic | Context-specific |
| Business control | Limited | Centralized |
| User experience | Interruptive | Seamless |
Use Cases Driving Embedded VPN Adoption
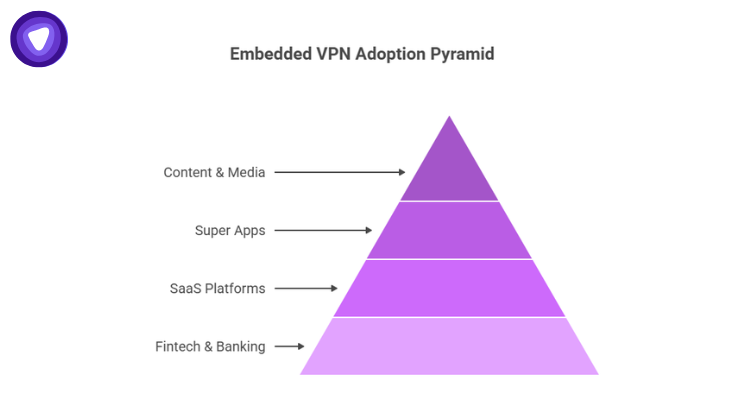
Embedded VPN adoption is accelerating in sectors where sensitive data flows continuously and cannot depend on user-controlled security tools.
1. Fintech and Digital Banking
Financial platforms handle sensitive transactions on untrusted networks.
Embedded VPNs ensure:
- End-to-end encryption within the app
- Protection against session hijacking
- Consistent security across devices
Given that the IBM Cost of a Data Breach Report places the average breach cost at $4.88 million, financial platforms prioritize built-in protection over optional tools.
2. SaaS Platforms with Distributed Teams
Remote work introduces:
- Multiple access points
- Unsecured home networks
- Device variability
Embedded VPNs allow SaaS platforms to:
- Control access to internal tools
- Segment traffic by role
- Maintain secure collaboration
3. Super Apps and Multi-Service Platforms
Super apps combine multiple services into one ecosystem.
This creates a challenge: securing internal data movement across features.
Embedded VPNs:
- Encrypt communication between services
- Protect user sessions across modules
- Maintain consistent privacy without user action
4. Content and Media Platforms
Platforms that manage global content access use embedded VPN logic to:
- Control regional availability
- Prevent unauthorized access
- Maintain compliance with licensing requirements
This eliminates the need for users to rely on external VPN tools.
The Business Case for Embedded VPN
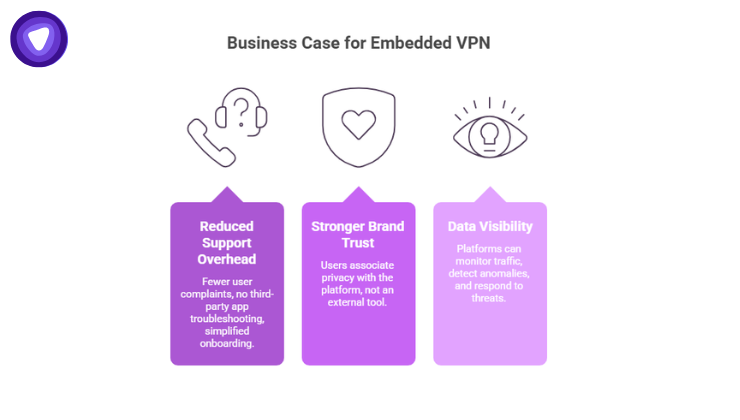
Beyond security, embedded VPNs offer operational advantages.
Reduced Support Overhead
- Fewer user complaints about connectivity
- No need to troubleshoot third-party apps
- Simplified onboarding
Stronger Brand Trust
Users associate privacy with the platform itself, not an external tool.
Data Visibility
Embedded solutions allow platforms to:
- Monitor traffic patterns
- Detect anomalies
- Respond to threats in real time
Standalone VPNs often obscure visibility instead of enhancing it.
Challenges in Implementation
Embedded VPNs are not plug-and-play.
Key challenges:
- Infrastructure complexity
- Scalability requirements
- Integration with existing systems
- Performance optimization
Building a secure, scalable embedded VPN layer requires expertise in:
- Network architecture
- Encryption protocols
- Traffic routing
- Access management
This is where many companies hesitate.
Where White Label VPN Fits in Embedded Security Architecture
White label VPN solutions provide a practical path for platforms that need embedded VPN functionality without building and maintaining complex networking infrastructure in-house. This approach is especially relevant for SaaS platforms, fintech applications, and digital ecosystems where secure connectivity is a core part of the product experience.
Instead of developing server networks, encryption layers, and routing logic internally, companies integrate a pre-built VPN framework directly into their applications while still maintaining platform-level control and secure connectivity.
PureVPN’s white label VPN solution enables businesses to embed secure networking directly into their platforms without managing backend infrastructure complexity. It supports custom integration into applications and services, scalable server infrastructure, secure global data routing, and full control over branding and user experience. This allows platforms to deliver privacy as a native feature rather than an external tool, aligning with the broader shift toward embedded security in modern digital products.
Final Thoughts
The role of VPNs is not shrinking; it is evolving with how modern software is designed and deployed. Standalone VPN applications introduced user-controlled privacy, where protection depends on manual activation and consistent usage. Embedded VPN models shift this responsibility to platforms, where security is enforced automatically and consistently across all interactions.
This shift reflects a broader architectural direction in software development. Security is increasingly designed to operate in the background, systems are being built to reduce reliance on user actions, and platforms are taking direct ownership of data protection across workflows. As a result, privacy is no longer treated as a separate tool that users manage, but as an integrated function of the system itself.
Users now expect privacy to be active by default, without configuration or intervention. Platforms that align with this expectation will define how secure digital experiences are delivered in the next phase of product development.


