- Vect Overview: Vect is a ransomware-as-a-service group that can encrypt and in some cases permanently destroy files across Windows, Linux, and ESXi systems.
- Critical Risk: Unlike traditional ransomware, Vect’s encryption flaw can make recovery impossible even after ransom payment.
- Threat Shift: The group reflects a shift toward more destructive ransomware models that behave closer to data-wiping attacks.
- Broader Trend: Vect highlights evolving cybercrime patterns, including faster deployment, supply chain involvement, and wider infrastructure targeting.
- Defense Focus: Security now depends on prevention-first strategies such as secure remote access, segmentation, isolated backups, and rapid detection.
Most ransomware groups follow a familiar pattern. They steal data, encrypt systems, demand payment, and promise recovery afterward.
Vect changed that model.
First spotted in late 2025, Vect quickly became one of the most concerning ransomware threats of 2026 after researchers discovered that Vect 2.0 was permanently destroying files instead of just encrypting them.
Unlike traditional ransomware, recovery is often impossible. A flaw in the malware’s encryption process corrupts files larger than roughly 128 KB, making them unrecoverable even if victims pay the ransom.
The result is ransomware that behaves more like a wiper attack.
Vect’s rise also reflects a broader shift in cybercrime. Ransomware groups are moving faster, targeting Linux and ESXi systems, partnering with supply chain actors, and expanding affiliate operations aggressively.
What Is Vect Ransomware?
Vect is a ransomware-as-a-service, or RaaS, operation first observed on Russian-language cybercrime forums in December 2025. The group began advertising affiliate recruitment shortly afterward and claimed its first victims in early 2026.
Like other RaaS operations, Vect provides ransomware infrastructure to affiliates who carry out attacks. Affiliates gain access to ransomware builders, management panels, and deployment tools while operators receive a share of ransom payments.
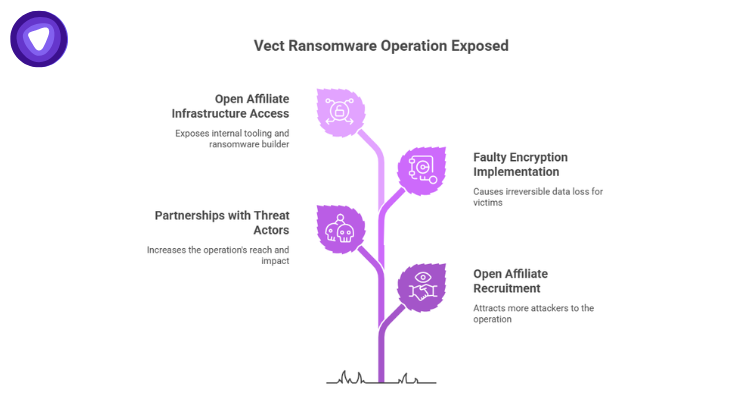
Researchers identified several characteristics that made Vect stand out quickly:
- Multi-platform targeting across Windows, Linux, and VMware ESXi
- Open affiliate recruitment strategies
- Partnerships with known threat actors
- Extremely fast encryption routines
- Faulty encryption implementation causing irreversible data loss
Security researchers gained access to Vect’s affiliate infrastructure after the group openly offered affiliate access through BreachForums. That unusual openness exposed large parts of the operation’s internal tooling and ransomware builder.
The investigation revealed serious technical flaws inside Vect 2.0.
Why Vect Is More Dangerous Than Typical Ransomware
Most ransomware is designed to preserve the ability to decrypt files after payment. Criminal groups depend on maintaining that reputation because future victims are more likely to pay if recovery appears possible.
Vect broke that model.
Researchers found that Vect mishandles encryption “nonces,” which are random values required to properly decrypt encrypted data. During encryption of larger files, the malware overwrites those values repeatedly, permanently corrupting the file structure.
That means:
| Traditional Ransomware | Vect 2.0 |
| Files are encrypted | Files are often destroyed |
| Recovery may work after payment | Recovery becomes impossible |
| Attackers keep decryption keys | Critical encryption data is lost |
| Extortion is the primary goal | Data destruction becomes the outcome |
Files larger than approximately 128 KB are especially vulnerable. According to researchers, that threshold includes most modern business documents, databases, backups, spreadsheets, virtual machine files, and email archives.
This changes the impact of an attack significantly.
Organizations facing Vect infections are not dealing with temporary operational disruption. They are dealing with permanent data loss.
The Rise of Multi-Platform Ransomware
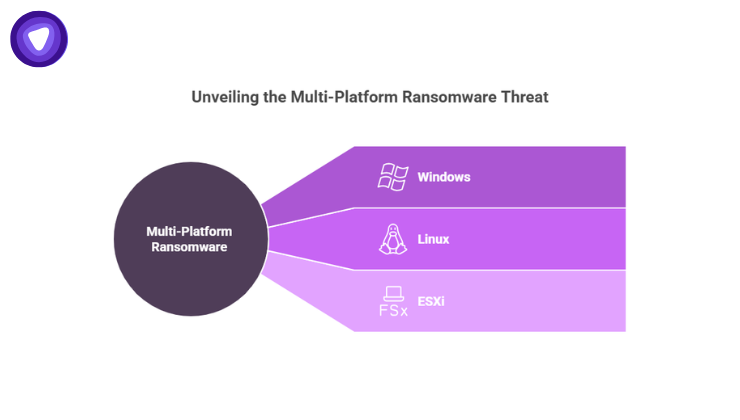
Older ransomware campaigns focused heavily on Windows environments.
Vect targets Windows, Linux, and ESXi systems simultaneously.
That reflects a larger industry trend. Attackers increasingly target virtualization infrastructure because it allows them to cripple multiple workloads through a single compromise.
VMware ESXi environments are especially attractive because:
- One encrypted host can impact dozens of virtual machines
- Many organizations centralize critical workloads on ESXi
- Recovery becomes slower and more expensive
- Backup repositories are often connected to the same infrastructure
Linux servers are also becoming a larger ransomware target due to their widespread use in cloud hosting, development infrastructure, and enterprise applications.
This broader targeting strategy increases operational damage while reducing the amount of effort attackers need to expend.
Supply Chain Connections Raise Additional Concerns
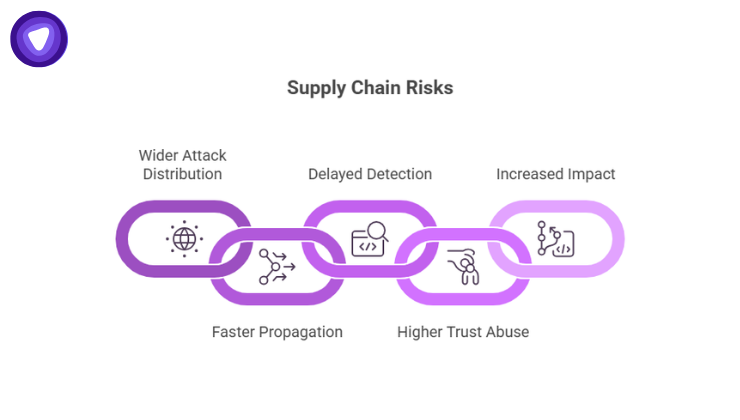
Vect gained even more attention after reports linked the group to TeamPCP, a threat actor associated with supply chain compromises involving tools like Trivy, LiteLLM, and Telnyx-related infrastructure.
That partnership matters because supply chain attacks scale rapidly.
Instead of compromising one organization directly, attackers compromise trusted software components or dependencies used by many organizations downstream.
Security teams have already seen the impact of this strategy in previous campaigns involving software repositories, package managers, and development pipelines.
The combination of ransomware deployment with supply chain compromise creates several risks:
- Wider attack distribution
- Faster propagation across environments
- Delayed detection
- Higher trust abuse
- Increased impact on software development ecosystems
This is particularly concerning for organizations running open source infrastructure or large CI/CD environments.
Why Ransomware-as-a-Service Keeps Growing

Vect is part of a broader ransomware economy that continues expanding despite increased law enforcement activity.
The ransomware-as-a-service model lowers the barrier to entry for cybercriminals. Operators develop the malware while affiliates focus on distribution and access.
This specialization increases attack volume.
According to the IBM Cost of a Data Breach Report 2025, the average global data breach cost reached $4.88 million. Ransomware continues to remain one of the most financially damaging attack categories for businesses worldwide.
Meanwhile, ransomware groups are evolving operationally:
- Faster encryption speeds
- More automation
- Cross-platform malware support
- Double extortion tactics
- Data destruction capabilities
- Supply chain integration
Vect demonstrates another emerging issue: attackers are releasing malware faster than they can properly test it.
Researchers analyzing Vect noted multiple coding flaws beyond the encryption bug, including thread handling problems and broken obfuscation routines. Some analysts even suggested portions of the malware may have been generated using AI-assisted coding tools.
That creates unpredictable outcomes for victims.
Common Initial Access Methods Used by Emerging Ransomware Groups

Vect affiliates appear to follow many of the same initial access patterns seen across modern ransomware campaigns.
Researchers observed activity linked to compromised Fortinet accounts and perimeter access sourcing on cybercrime forums.
Common entry points include:
Stolen Credentials
Weak passwords, reused credentials, and exposed VPN accounts remain major attack vectors.
Unpatched Remote Access Systems
VPN gateways, firewalls, and remote desktop services are frequent ransomware entry points when vulnerabilities remain unpatched.
Phishing Campaigns
Credential theft through phishing continues to drive initial compromise activity across enterprise environments.
Supply Chain Compromise
Compromised software dependencies allow attackers to bypass traditional perimeter defenses entirely.
Credential abuse and phishing remain among the most common attack vectors across ransomware incidents.
What Businesses Should Learn From Vect
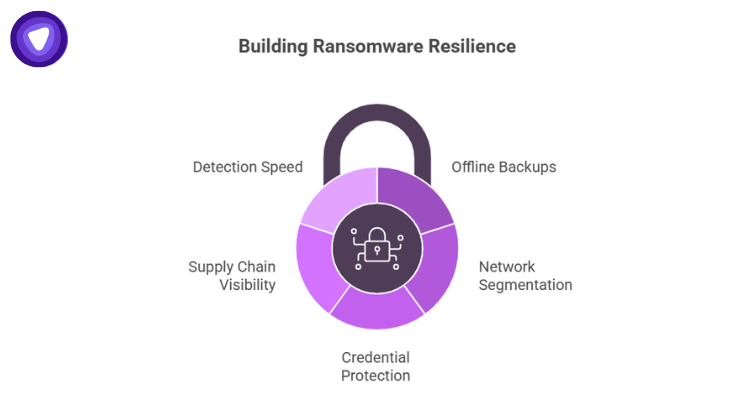
Vect highlights an uncomfortable reality about modern ransomware defense.
Recovery cannot depend solely on paying attackers.
Organizations now need resilience strategies that assume:
- Decryption may fail
- Data may be permanently destroyed
- Backup infrastructure may be targeted
- Multiple operating systems may be affected simultaneously
Several defensive priorities stand out.
Offline Backups Matter More Than Ever
Backups remain one of the strongest ransomware defenses, but only when they are isolated and regularly tested.
Connected backups are increasingly targeted during attacks.
Network Segmentation Reduces Blast Radius
Separating critical systems limits lateral movement during compromise.
This becomes especially important in virtualized environments.
Credential Protection Is Essential
Multi-factor authentication, privileged access controls, and credential monitoring reduce exposure from stolen accounts.
Supply Chain Visibility Needs Improvement
Organizations need better visibility into third-party dependencies, software packages, and development pipeline risks.
Detection Speed Directly Impacts Damage
Research published in 2026 showed behavioral ransomware detection systems identifying threats within roughly 9 seconds during testing environments.
Early detection increasingly determines whether ransomware reaches critical infrastructure before containment begins.
Where Secure Remote Access Fits Into Ransomware Defense
Many ransomware campaigns begin with exposed remote access infrastructure.
Compromised VPN credentials, insecure remote desktop services, and poorly segmented remote connections continue to provide attackers with reliable entry points.
This is where businesses are shifting toward more controlled remote access strategies.
Solutions like PureVPN White Label VPN Solution allow organizations, service providers, and platforms to build branded secure access environments while maintaining encrypted connections and centralized access management.
For businesses managing distributed teams, development environments, or customer-facing platforms, secure remote connectivity reduces exposure tied to unsecured access paths and credential abuse. Features such as Dedicated IP support, encrypted tunnels, and controlled network access help limit common ransomware entry vectors.
The growing focus is no longer just connectivity. It is reducing unnecessary exposure across remote infrastructure.
The Bigger Shift Behind Vect
Vect may still be an emerging ransomware group, but it reflects several larger cybersecurity trends already reshaping enterprise risk. Ransomware operations are becoming faster to launch, easier to distribute, more automated, and increasingly destructive. Attackers are also expanding beyond Windows environments, targeting Linux servers, virtualization platforms, and remote access infrastructure more aggressively.
Vect also exposed another reality about modern ransomware. Poorly coded malware can cause permanent damage regardless of ransom payment. For organizations, ransomware defense can no longer depend on negotiation or recovery promises from attackers. The priority has shifted toward prevention, network segmentation, secure remote access, isolated backups, and faster threat detection.


