- ARP is critical but insecure: The Address Resolution Protocol translates IP addresses to MAC addresses for local network communication but lacks built-in authentication or encryption.
- ARP spoofing and cache poisoning are major threats: Attackers can manipulate ARP tables to intercept, modify, or drop network traffic.
- ARP-based DoS and reconnaissance attacks are common: Malicious ARP replies can disrupt traffic or reveal network devices to attackers.
- Mitigation requires multiple layers: Using static ARP entries, dynamic ARP inspection, network segmentation, monitoring, and encrypted traffic reduces risk.
- VPN solutions enhance ARP security: Implementing encrypted, identity-based access through a VPN, like PureVPN White Label, protects sensitive data even if ARP vulnerabilities exist on the local network.
Before you ever typed a URL or opened an application, the humble Address Resolution Protocol (ARP) was quietly doing its job, translating IP addresses to MAC addresses so your devices can communicate on a local network. But as networks scale and threat actors get more sophisticated, ARP’s fundamental design weaknesses have become a serious security liability.
In this blog, we will discuss the key Address Resolution Protocol vulnerabilities that businesses should be aware of in 2025, explain exactly how ARP works, and highlight mitigation strategies, including how a White Label VPN Solution can play a role.
What Is the Address Resolution Protocol?

Diagram showing how ARP maps IP addresses to MAC addresses through ARP requests and replies on a local network.
To understand its risks, you first need to understand what ARP is and how it works. This foundational understanding sets the stage for why ARP vulnerabilities are so dangerous, and why businesses must take them seriously.
- Address resolution protocol definition: ARP is a protocol used in computer networks (specifically in IPv4 networks) to map a network-layer IP address to a link-layer MAC address.
- Address resolution protocol explained: When Device A wants to talk to Device B on the same LAN but only knows B’s IP, A broadcasts an address resolution protocol request, asking, “Who has this IP? Tell me your MAC.” The device with that IP replies with its MAC in an ARP reply. That mapping is stored in A’s ARP cache (also called an ARP table).
- Address resolution protocol port number: Because ARP works at the data-link layer (Layer 2), it does not use TCP or UDP ports like higher-level protocols; it operates independently of the TCP/UDP port model.
Understanding how ARP resolution works leads directly into why ARP tables become a critical security control and a target.
What Is an ARP Table and How Does It Work?
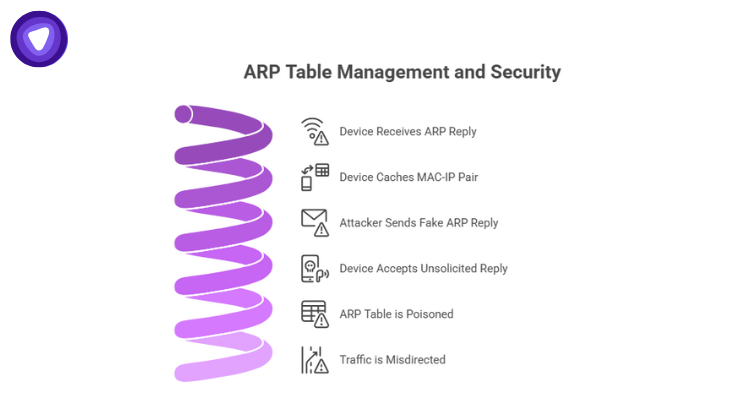
An ARP table, sometimes called the ARP cache, is where devices store IP-to-MAC mappings. This is vital for efficient communication on a LAN.
- When a device receives an ARP reply, it caches that MAC–IP pair in its ARP table for faster future lookups.
- Because ARP is stateless, devices accept unsolicited ARP replies, which means an attacker can send a fake ARP reply and poison the table.
- Devices rely on the ARP table to forward Ethernet frames, if an entry is maliciously altered, traffic can be misdirected or intercepted.
By grasping the mechanics of the ARP table, we gain insight into how attacks exploit this core structure.
Types of Address Resolution Protocol (ARP) & Related Protocols

ARP isn’t one-size-fits-all. Several variants and related protocols are used in different contexts, each with its own implications and risk.
- Standard ARP: the basic form: IP → MAC mapping.
- Gratuitous ARP: a device broadcasts a reply without being asked, often for conflict detection or announcing a new MAC.
- Proxy ARP: a router or intermediary answers ARP on behalf of another device.
- Reverse Address Resolution Protocol (RARP): Works in reverse, you give the MAC, and it returns an IP. Once used for diskless workstations, it’s now mostly obsolete, replaced by DHCP. Understanding these types helps clarify how reverse address resolution protocol in computer networks plays a (diminished) role in modern networks.
Recognizing these variants is essential for diagnosing and mitigating address resolution protocol vulnerabilities in different networking environments.
Why Address Resolution Protocol Is Used And Why It’s Risky

ARP is foundational to network communication, but its design compromises security for simplicity.
Address resolution protocol is used for:
- Enabling devices on the same LAN to communicate by resolving IPs into MAC addresses.
- Reducing broadcast traffic by caching mappings in ARP tables.
However, the protocol has serious drawbacks:
- There is no authentication: any device can respond to an ARP request, and replies are blindly trusted.
- It’s stateless: ARP replies do not require prior requests, meaning malicious ARP packets can be injected at will.
- It lacks encryption or integrity checks: all ARP messages are in plaintext, and there’s no verification mechanism to ensure they are genuine.
This combination of trust and simplicity makes ARP a ripe target for attackers.
Major ARP Vulnerabilities Every Business Must Know in 2025

Before diving into the specifics of ARP spoofing, it’s important to understand that ARP vulnerabilities are not isolated incidents, they form part of a broader set of risks that can compromise the integrity, confidentiality, and availability of network communications.
1. Address Resolution Protocol Spoofing (ARP Poisoning)
One of the most dangerous vulnerabilities facing networks today.
- An attacker sends fake ARP replies to associate their MAC with a trusted IP, often the gateway.
- Because devices accept these forged replies, the attacker can perform a man-in-the-middle (MITM) attack: intercepting, modifying, or dropping traffic.
- Real-world forensics research shows this isn’t theoretical, a 2025 study on MikroTik routers demonstrated how ARP cache entries could be manipulated, confirming MITM-style redirection under controlled conditions.
These spoofing attacks remain a foundational risk for LAN-based exploitation.
2. ARP Cache Poisoning
Closely tied to spoofing, poison attacks corrupt ARP tables.
- Attackers send unsolicited (gratuitous) ARP messages to replace valid entries with malicious ones.
- Because ARP entries persist in cache until they expire, a poisoned mapping can persist long enough for significant harm.
- A poisoned ARP cache can lead not just to interception, but to denial-of-service (DoS) scenarios if traffic gets misrouted or dropped.
Cache poisoning remains a favored technique for adversaries seeking persistent or stealthy control.
3. ARP Denial of Service (DoS)
ARP misuse isn’t just about eavesdropping, it can also disrupt.
- Attackers reply with bogus ARP entries that map critical IPs (e.g., a router) to a non-existent MAC address, causing legitimate devices to send traffic into a void.
- Because ARP operates at Layer 2, these DoS attacks may not trigger typical higher-layer security controls.
- The result can be widespread network instability without obvious indicators, especially in flat broadcast domains.
This attack vector underscores just how multipurpose ARP vulnerabilities can be.
4. Reconnaissance via ARP Scanning
Even without active attacks, ARP can be used for intelligence gathering.
- Attackers broadcast ARP requests across a subnet to discover which IP addresses are in use (live hosts).
- From responses, they can infer MAC address vendor data, device types, and potential valuable targets.
- In one sense, this is “low noise” but high-value: identifying potential targets before mounting more advanced attacks.
This reconnaissance may seem benign, but it’s often a precursor to more serious exploitation.
Reverse Address Resolution Protocol (RARP) & Its Role in Vulnerabilities

Even though rarely used now, reverse address resolution protocol deserves a brief look.
- What is RARP: RARP allows a machine to obtain its IP address by broadcasting its MAC.
- Security risk: Legacy devices or poorly maintained networks that still use RARP lack modern protections and can be more predictable targets.
- Modern relevance: Today, DHCP has replaced RARP in almost all enterprise environments, reducing but not totally eliminating risk in older systems.
Recognizing RARP’s place in historical networks helps when auditing older infrastructure.
Real‑World Consequences: Address Resolution Protocol Example Scenarios
Let’s look at some address resolution protocol example scenarios to illustrate real business risk.
| Scenario | Risk | Impact |
| BYOD-heavy office LAN | A compromised personal device spoofs ARP for the default gateway | MITM attack, internal traffic compromised |
| Large IoT deployment | Unsecured sensors spoof ARP | Data interception, device manipulation |
| Flat (unsegmented) network | Attacker launches ARP scan then spoofing | Full network visibility and control |
| Legacy devices | Use of RARP for IP discovery | Predictable behavior, device impersonation |
These examples show how ARP vulnerabilities aren’t just theoretical, they equally threaten modern and legacy infrastructure.
How an Attack Plays Out

Here is a simplified address resolution protocol diagram (described in text form) of a common ARP spoofing attack:
- The attacker observes a device (Victim) send an ARP request: “Who has IP X?”
- The attacker immediately sends a spoofed ARP reply, claiming “I have IP X, here’s my MAC.”
- The victim updates its ARP table, associating the attacker’s MAC with the IP.
- Traffic destined for IP X now flows through the attacker’s device (MITM).
- The attacker intercepts, inspects, modifies, or even drops the traffic before relaying it.
This flow shows exactly why ARP spoofing can be devastating because of that blind trust built into ARP’s design.
Address Resolution Protocol Configuration & Mitigation
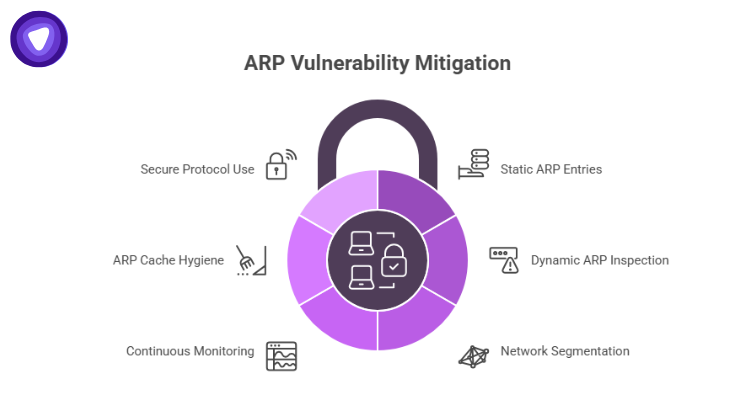
Mitigating ARP vulnerabilities requires a layered approach. Here are practical steps:
- Static ARP Entries
- For mission-critical devices (servers, routers), manually configure static IP–MAC mappings.
- While not scalable for all devices, static entries eliminate the risk of dynamic poisoning.
- For mission-critical devices (servers, routers), manually configure static IP–MAC mappings.
- Dynamic ARP Inspection (DAI)
- Deploy managed switches that support DAI. DAI validates ARP traffic against a trusted binding table (often built from DHCP).
- If a switch sees an ARP packet that doesn’t match the binding table, it drops it, preventing spoofing.
- Deploy managed switches that support DAI. DAI validates ARP traffic against a trusted binding table (often built from DHCP).
- Network Segmentation
- Use VLANs to separate vulnerable devices (e.g., guest BYOD, IoT) from critical infrastructure.
- Limiting the broadcast domain reduces the reach of any ARP-based attack.
- Use VLANs to separate vulnerable devices (e.g., guest BYOD, IoT) from critical infrastructure.
- Continuous Monitoring & Detection
- Leverage ARP spoofing detection tools. Researchers are now using machine learning models that can flag anomalies in ARP header behavior or timing.
- According to a 2025 study, a multi-layered ML detection system achieved over 97% detection accuracy for ARP spoofing in IoT environments.
- Leverage ARP spoofing detection tools. Researchers are now using machine learning models that can flag anomalies in ARP header behavior or timing.
- ARP Cache Hygiene
- Periodically flush ARP tables across devices to remove stale or possibly malicious entries.
- Monitor for sudden or repeated changes in IP–MAC mappings as a sign of potential attacks.
- Periodically flush ARP tables across devices to remove stale or possibly malicious entries.
- Secure Protocol Use
- Implement cryptographic enhancements like S-ARP, which attaches message authentication to ARP, thwarting spoofing.
- Encrypt internal traffic (e.g., via VPN) to ensure that even if ARP is compromised, the attacker cannot easily read or modify the data.
- Implement cryptographic enhancements like S-ARP, which attaches message authentication to ARP, thwarting spoofing.
Address Resolution Protocol Program in C (Brief Overview)
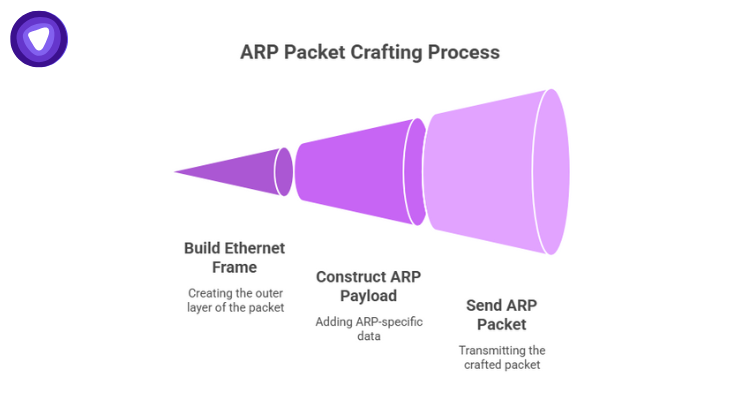
For network engineers or developers: writing a simple ARP program in C can deepen understanding or be used for testing defenses.
- Use raw sockets to build Ethernet frames: specify destination MAC, source MAC, and EtherType = 0x0806 (ARP).
- Construct the ARP payload: hardware type (Ethernet), protocol type (IPv4), the opcode (request or reply), and sender/target MAC and IP fields.
- Send crafted ARP request or reply packets. This mimics both genuine resolution and address resolution protocol spoofing, allowing you to simulate attack conditions in a lab.
Emerging Threats & Trends Around ARP in 2025
ARP security isn’t just a legacy concern, new trends are making it more relevant:
- IoT growth: With IoT attacks rising sharply for instance, IoT malware attacks surged by 107% in the first half of 2024 compared to 2023. Many of these devices have weak or no built-in ARP protections.
- AI-driven detection: As mentioned, multi-layered machine learning systems are emerging, a 2025 paper demonstrated over 97% accuracy in detecting ARP spoofing.
- Rise of zero-trust architecture: More organizations are shifting to zero-trust designs. Yet, if ARP vulnerabilities remain in the local network, they can undermine these strategies.
- Hybrid networks & remote access: As businesses blend on-premise, cloud, and remote infrastructures, untrusted segments feed into local ARP risk.
These trends show that ARP is not a relic, it is a live threat surface, especially in modern distributed environments.
How PureVPN White Label VPN Solution Helps Mitigate ARP Risks
While many ARP vulnerabilities are local‑network issues, PureVPN White Label VPN Solution addresses risk in complementary ways:
First, by enforcing encrypted tunnels, PureVPN ensures that even if an attacker compromises ARP in a LAN (via spoofing or poisoning), they cannot read or tamper with the data in transit. The encryption adds a strong layer of confidentiality and integrity.
Second, the VPN enables segmentation and identity-based access. With PureVPN White Label, businesses can restrict critical system access (e.g., administrative consoles, internal tools) to devices that connect via authenticated VPN only. This isolation reduces the exposure of sensitive traffic to local ARP-based threats.
Final Thoughts
In short: combining ARP-level defenses with VPN-level security significantly lowers your risk, especially for hybrid or remote environments.
The Address Resolution Protocol is deceptively simple, but in 2025, its lack of built-in security makes it a persistent and serious risk. From spoofing and cache poisoning to DoS and reconnaissance, ARP-based attacks remain a favorite vector for adversaries who exploit trust at the local network layer.
A solid defense demands multiple layers: static configuration, dynamic inspection, monitoring, and intelligent responses. But strong ARP protection alone is not enough, combining it with encrypted, identity-based access through a solution like PureVPN White Label VPN can dramatically heighten your security posture.