The moment a VPN provider starts recording activity data, the promise of privacy begins to erode. For users, that distinction is rarely visible. A VPN interface looks the same whether it protects privacy or quietly stores browsing information behind the scenes. The difference lies in one place most users never see: the logging policy.
- Logging Policies: Define how user data is handled and affect privacy, transparency, and credibility of VPN services.
- Log Types: Distinguishing activity logs, connection logs, and no-log policies helps align VPN services with privacy expectations.
- Risks: Poor logging exposes users to surveillance, legal issues, and damages brand reputation.
- Transparency: Clear logging policies build user trust amid growing cybersecurity threats and privacy concerns.
- Operational Balance: Businesses must configure logging to protect user privacy while meeting service and operational needs.
For businesses launching VPN services through white label platforms, logging policies shape how user data is handled and how privacy claims are validated. Poor logging practices can expose users to surveillance risks and damage brand credibility, while clear, well-defined policies strengthen transparency and trust.
Understanding these policies is essential for anyone building or managing a VPN service.
What Logging Means in a VPN Environment
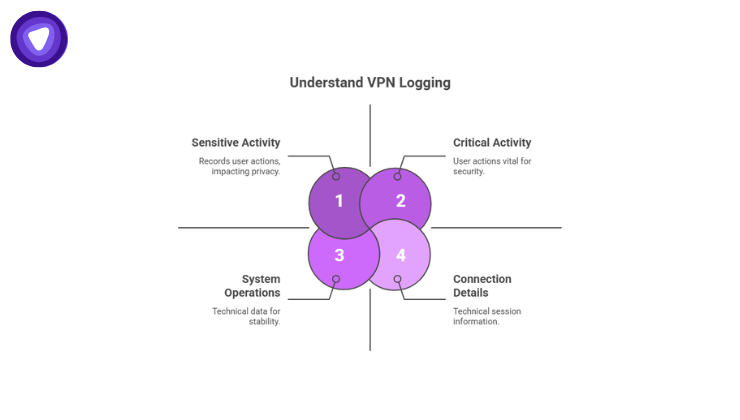
VPN logging refers to the collection and storage of data related to user activity, connection details, or system operations within a VPN network.
Not all logs are the same. Some support service performance and security operations, while others record sensitive user behavior.
Logging categories generally fall into three groups:
1. Activity Logs
Activity logs record what users do while connected to the VPN.
Examples include:
- Websites visited
- DNS queries
- Download activity
- Browsing history
- Application usage
These logs directly contradict the privacy promise associated with VPN services. Most privacy-focused VPN providers avoid storing them entirely.
2. Connection Logs
Connection logs track technical session information rather than browsing behavior. Typical data includes:
- Connection timestamps
- Session duration
- Server location used
- Amount of bandwidth consumed
- Device or IP metadata
Some VPN providers maintain limited connection logs for operational reasons such as preventing abuse or balancing network resources.
3. System Logs
System logs focus on infrastructure performance and security monitoring.
Examples include:
- Server performance data
- Authentication errors
- System diagnostics
- Network performance metrics
These logs help operators maintain stability without collecting user activity information.
Why Logging Policies Matter for White Label VPN Providers
Launching a VPN service through a white label platform means the infrastructure already exists, but the responsibility for privacy claims remains with the brand operating the service.
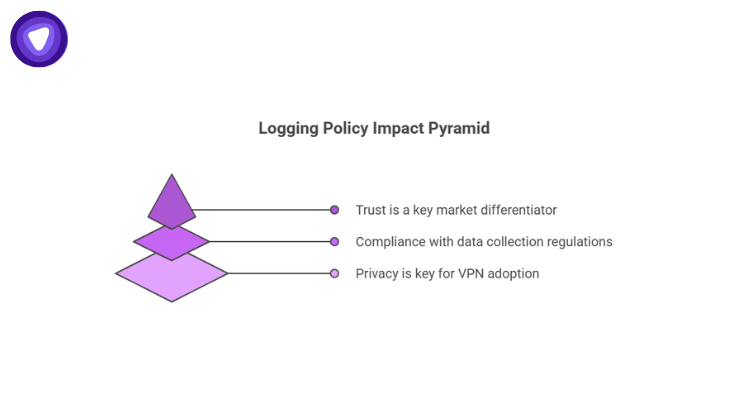
Logging policies influence three major factors.
1. User Trust
Privacy is the primary reason users adopt VPN technology. A service that collects excessive logs undermines its own value.
According to Statista, global VPN usage exceeded 1.6 billion users in 2024, driven largely by privacy concerns and security awareness. As the market expands, users increasingly evaluate providers based on transparency and data protection policies.
A clear logging policy communicates how user information is handled and what data is never stored.
2. Legal and Regulatory Exposure
Many jurisdictions require companies to explain what data they collect and how long it is stored.
A vague or misleading logging policy can lead to legal consequences if the service collects more data than disclosed.
A study found that 94% of organizations report customers will not buy from them if data protection is inadequate. Transparency around logging practices therefore influences both compliance and customer acquisition.
3. Brand Reputation
White label VPN operators compete in a market where trust is a major differentiator. If a provider’s logging practices are exposed or misunderstood, reputation damage spreads quickly.
Public scrutiny of privacy services has increased over the past decade, and users expect detailed documentation about logging behavior.
The Difference Between No-Log and Minimal-Log Policies
The terms “no-log” and “minimal-log” often appear in VPN marketing, but they represent different technical approaches.
| Logging Policy Type | Data Stored | Privacy Impact | Common Use Case |
| No-Log Policy | No activity or connection logs stored | Highest privacy protection | Privacy-focused VPN services |
| Minimal Connection Logs | Temporary connection timestamps or bandwidth data | Limited privacy exposure | Network management and abuse prevention |
| Extensive Logging | Activity logs, browsing data, IP tracking | Significant privacy risk | Monitoring-heavy networks |
A true no-log approach means user activity cannot be reconstructed even if systems are examined or requests for data are made.
Minimal-log systems attempt to balance operational management with privacy protection, but they must clearly define what data is collected and when it is deleted.
Infrastructure Factors That Influence Logging
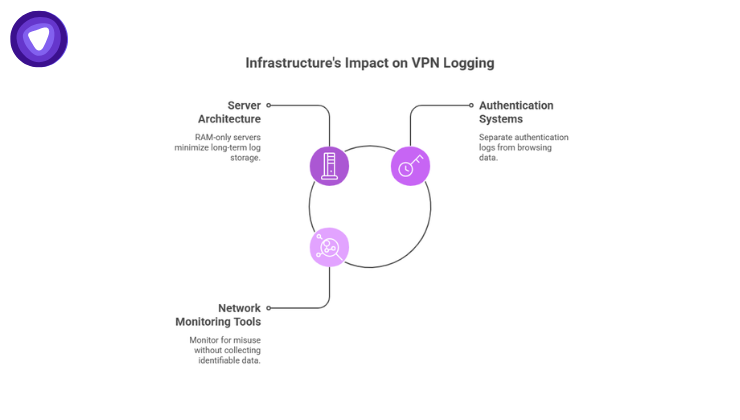
Logging policies are not only legal statements. They are directly shaped by the technical architecture of the VPN network.
White label platforms must align their infrastructure design with their privacy claims.
Server Architecture
Servers can be configured to store logs locally or operate in memory-based environments.
Some privacy-focused networks use RAM-only servers, meaning data disappears automatically whenever the system restarts.
This design significantly reduces the risk of long-term log storage.
Authentication Systems
User authentication systems sometimes generate logs during login attempts or session verification.
These logs can include:
- Login timestamps
- Failed login attempts
- Account status checks
Proper systems separate authentication records from browsing activity to prevent user tracking.
Network Monitoring Tools
Operators use monitoring tools to detect network misuse such as spam, bot activity, or denial-of-service attacks.
These tools must be configured carefully to avoid collecting identifiable browsing data while still protecting the network.
Transparency: The Most Important Element of Logging Policies
Users rarely read technical documentation in detail, but they expect clear answers about privacy.
A strong logging policy typically includes:
- A precise definition of what logs are not collected
- A list of any operational data that is collected
- The retention period for any stored logs
- The purpose of each log type
- Information about data jurisdiction
Transparency removes ambiguity and helps prevent misunderstandings between VPN providers and users.
Industry Trends Shaping VPN Logging Policies
The expectations surrounding VPN privacy have changed rapidly over the past few years.
Three major trends now influence how logging policies are structured.
Growing Global VPN Adoption
VPN adoption continues to rise across both personal and business environments.
A 2025 report estimates the VPN market will surpass $75 billion by 2027, reflecting growing concern about data privacy, surveillance, and cyber threats.
As adoption grows, so does scrutiny of privacy claims.
Increased Independent Audits
Many VPN providers now submit their infrastructure and logging policies to third-party security audits.
These audits verify that servers operate according to documented privacy policies. Independent validation has become one of the strongest signals of credibility in the VPN industry.
Rising Cybersecurity Threats
Cybercrime continues to escalate globally. Cybercrime damages are projected to reach $10.5 trillion annually worldwide, reinforcing the importance of secure internet infrastructure and private browsing environments.
VPN providers must balance strong privacy guarantees with network protection mechanisms.
Common Misconceptions About VPN Logging
Misunderstandings about logging policies often lead to unrealistic expectations or misleading marketing claims.
Myth 1: All VPNs Are Automatically No-Log
Many VPN services claim privacy protection, but their logging policies vary widely. Without documentation, it is impossible to verify how user data is handled.
Myth 2: Connection Logs Always Compromise Privacy
Connection logs do not necessarily reveal browsing activity. When limited to operational data and deleted quickly, they can help maintain service stability without exposing user behavior.
Myth 3: White Label VPN Platforms Limit Privacy Options
Modern white label VPN platforms allow operators to configure privacy settings, authentication systems, and server environments that support strong privacy policies.
The platform provides the infrastructure, but policy decisions still depend on the service provider.
How Businesses Should Evaluate White Label VPN Logging Policies

Organizations planning to launch a VPN service should examine logging capabilities carefully before selecting a white label platform.
Key evaluation factors include:
1. Log Collection Controls
The platform should allow operators to configure exactly what information is collected.
2. Data Retention Policies
Operators should be able to define how long logs remain stored and ensure automatic deletion when no longer required.
3. Server Architecture
Privacy-focused server environments such as RAM-based infrastructure reduce long-term log storage risks.
4. Security Monitoring Without Activity Tracking
The network should include mechanisms for preventing abuse while avoiding the collection of browsing data.
5. Documentation Transparency
Clear documentation helps operators communicate accurate privacy claims to their customers.
How PureVPN’s White Label Platform Approaches Logging
Businesses launching VPN services need infrastructure that supports transparent privacy practices without requiring them to build a network from scratch.
The PureVPN White Label VPN platform provides a ready-to-deploy VPN environment where service providers can launch branded VPN solutions while maintaining control over operational policies, including how logging practices are defined and communicated to users.
The platform offers global VPN server infrastructure, secure connectivity, and scalable deployment capabilities. This allows organizations to focus on building their service and user experience while relying on established infrastructure that supports strong privacy standards.
Final Thoughts
Logging policies define the real privacy boundary of any VPN service. Interfaces, encryption standards, and server locations all matter, but none of them determine privacy as clearly as the data a provider chooses to store.
For businesses entering the VPN market through white label platforms, logging policies must be carefully structured and transparently documented. Users expect clarity, regulators expect accountability, and the credibility of the service depends on both.
A well-designed logging framework protects user privacy, strengthens brand trust, and ensures the VPN service operates in alignment with the expectations that drive VPN adoption worldwide.


