- Yurei Ransomware Overview: Yurei ransomware is a stealth-based malware that encrypts data and steals sensitive information before triggering ransom demands.
- Infection Methods: It typically spreads through phishing emails, stolen credentials, exposed remote services, and weak authentication controls.
- Stealth Behavior: It stays hidden for long periods, uses legitimate system tools, and only encrypts data after gaining deep access inside networks.
- Attack Advantage: It combines data theft with encryption, meaning attackers can both lock systems and threaten to leak stolen information.
- Prevention: Organizations can reduce risk by strengthening access controls, using multi-factor authentication, segmenting networks, and securing remote access with encrypted connections.
A system rarely announces when it has been compromised. No alerts, no visible disruption, no obvious crash. Just normal operations continuing while an attacker quietly builds control in the background. Yurei ransomware is built around that silence. It stays hidden, moves laterally across networks, and strikes only after access is fully established.
The name “Yurei” comes from Japanese folklore, referring to restless spirits that linger unseen. The analogy fits the way this ransomware operates inside corporate environments.
What is Yurei Ransomware?
Yurei ransomware is a modern double-extortion malware strain first observed in 2025. It encrypts files across infected systems and steals sensitive data before encryption begins, creating pressure on victims from two directions: operational disruption and data exposure.
Security research shows that Yurei is built using modified open-source ransomware code, lowering the technical barrier for attackers while retaining strong encryption capabilities such as ChaCha20-based file locking and ECIES key wrapping.
Once deployed, it targets Windows environments and spreads across connected systems using credentials and shared network access.
How Yurei Infiltrates Systems
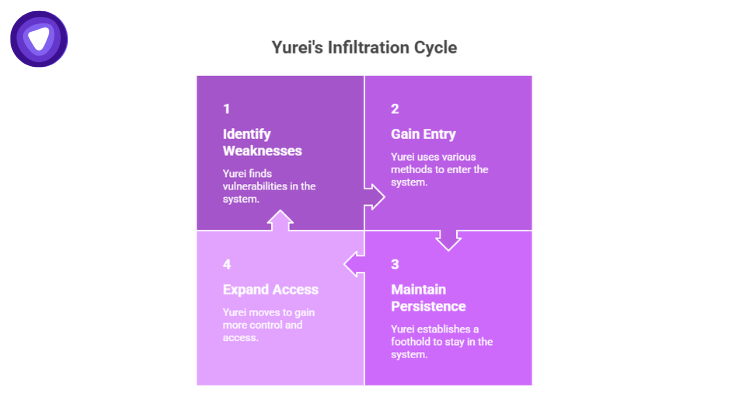
Yurei does not rely on a single entry point. It adapts based on exposed weaknesses inside an organization.
Common infection methods include:
- Phishing emails with credential theft payloads
- Stolen remote desktop credentials
- Exposed remote services without strong authentication
- Abuse of administrative tools such as PsExec and WMI
After entry, the malware avoids immediate encryption. Instead, it focuses on maintaining persistence and expanding access.
Inside the Attack Lifecycle
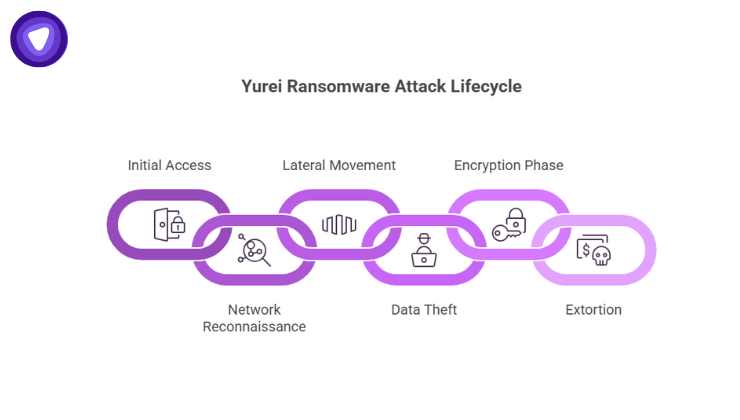
Yurei ransomware follows a structured sequence designed for stealth and maximum impact.
1. Initial access and stealth setup
Attackers enter using stolen or weak credentials and establish hidden persistence mechanisms.
2. Network reconnaissance
The malware scans internal systems, identifies high-value servers, and maps privilege structures.
3. Lateral movement
Attackers move across systems using valid credentials, often appearing as legitimate users.
4. Data theft
Sensitive files are extracted before encryption begins, including backups and internal documents.
5. Encryption phase
Files are locked using strong cryptographic methods, often with unique keys per file.
6. Extortion
Victims receive a ransom demand threatening both system recovery delays and public data leaks.
This dual strategy is now a standard feature in modern ransomware operations.
Why Yurei Is Hard to Detect
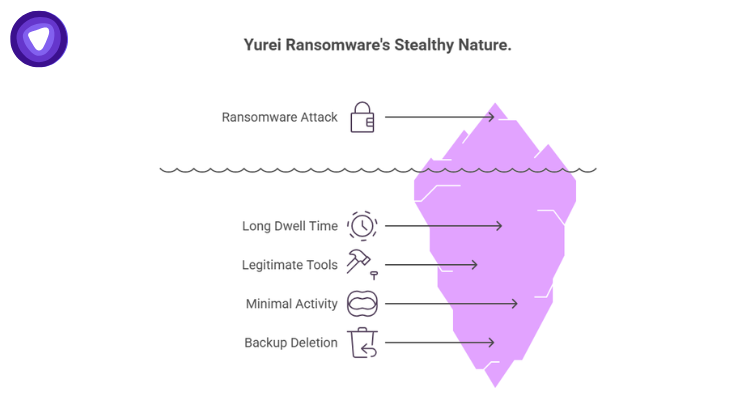
Yurei ransomware avoids early detection by minimizing visible system disruption. Instead of immediate encryption storms or system crashes, it operates quietly.
Key reasons detection is difficult:
- Long dwell time before encryption
- Use of legitimate system tools for movement
- Minimal early file activity
- Deletion or disabling of backup recovery mechanisms
Research indicates Yurei actively deletes Volume Shadow Copies and backup catalogs to prevent recovery.
This reduces the chances of rollback once encryption begins.
Technical Behavior and Encryption Model
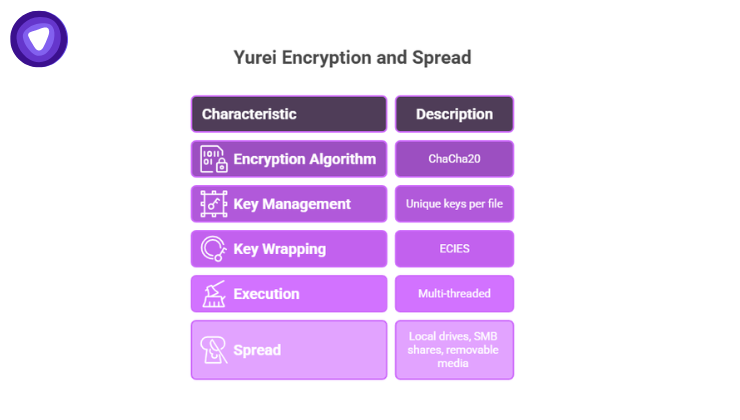
Yurei’s encryption process is designed for speed and reliability. Each file is encrypted using unique cryptographic keys, making mass decryption extremely difficult without attacker cooperation.
Key technical traits include:
- ChaCha20-based encryption per file
- Unique key and nonce generation for each file
- ECIES-based wrapping of encryption keys
- Multi-threaded execution for rapid encryption across drives
It also spreads across local drives, SMB shares, and removable media, ensuring wide coverage within minutes of activation.
Impact on Organizations
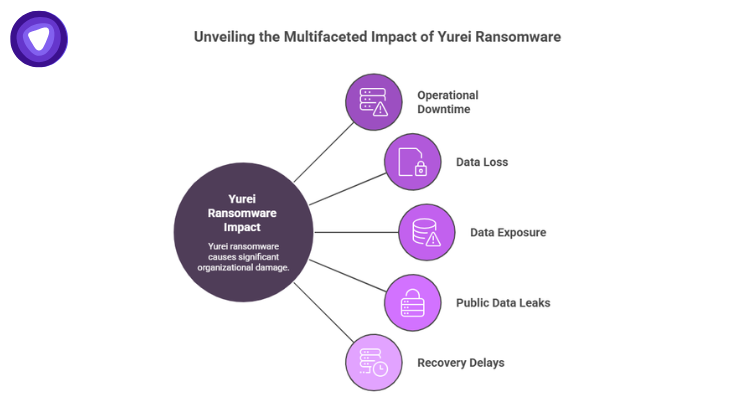
The real damage from Yurei ransomware is not limited to encryption.
Organizations face multiple layers of impact:
- Operational downtime across critical systems
- Loss of access to encrypted data
- Exposure of sensitive customer or business data
- Risk of public data leaks or resale
- Recovery delays due to destroyed backups
The global average cost of a data breach reached in 2025, reflecting the financial scale associated with incidents involving data theft and system compromise.$4.88 million
Ransomware now consistently ranks among the most expensive forms of cyber incidents for enterprises.
Yurei Ransomware Risk Breakdown
This structure shows why early detection is more effective than post-incident recovery.
| Stage | Primary Risk | Business Impact | Detection Difficulty |
| Initial access | Credential theft | Unauthorized entry | High |
| Persistence | Hidden control | Long-term compromise | High |
| Lateral movement | Internal spread | Domain-wide exposure | Critical |
| Data theft | Sensitive data leakage | Regulatory and reputational damage | Critical |
| Encryption | System lockout | Operational shutdown | Severe |
| Extortion | Financial pressure | Ransom demand + leakage threat | Severe |
Security Gaps Yurei Exploits
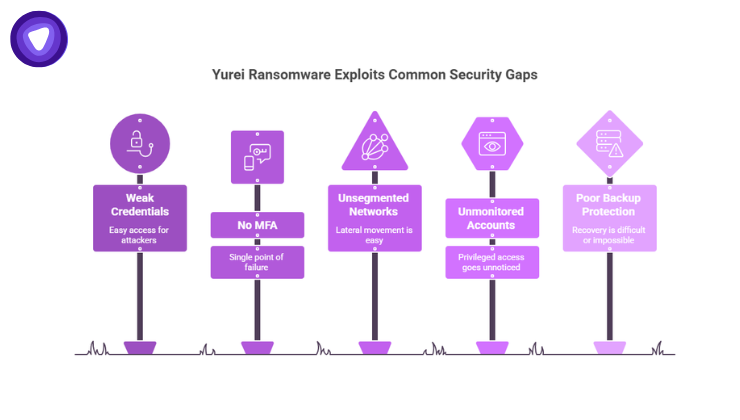
Yurei ransomware succeeds not through complexity alone but through common security gaps.
Frequent weaknesses include:
- Weak or reused credentials
- Lack of multi-factor authentication
- Unsegmented internal networks
- Unmonitored privileged accounts
- Inactive or poorly configured backup protection
Even basic access controls, when missing, allow attackers to escalate quickly.
How Organizations Reduce Exposure
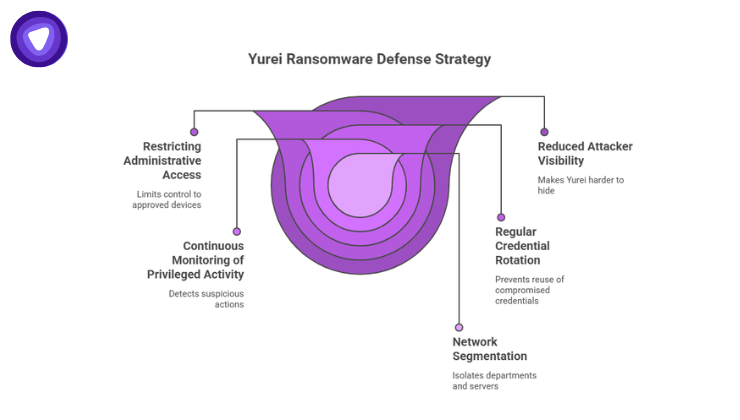
Defending against Yurei-style ransomware requires limiting both entry points and internal movement.
Core controls include:
- Strong identity verification for all remote access
- Multi-factor authentication on all critical systems
- Network segmentation between departments and servers
- Continuous monitoring of privileged activity
- Restricting administrative access to approved devices only
- Regular credential rotation and access audits
These measures reduce the attacker’s ability to remain invisible inside the network.
Secure Access as the First Barrier
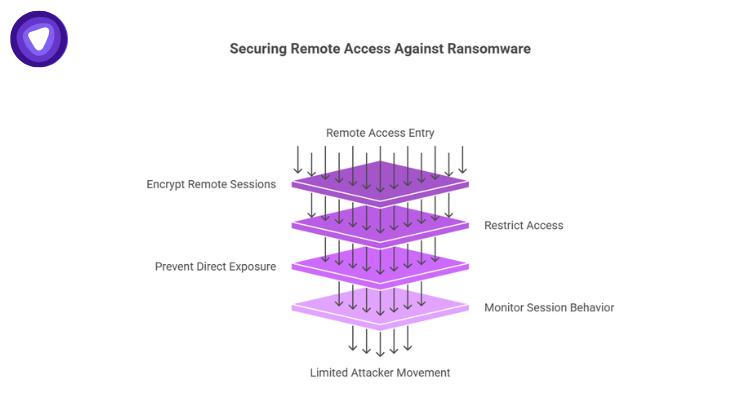
Remote access remains one of the most exploited entry paths in ransomware attacks. Yurei-style intrusions often begin with compromised remote credentials or exposed services.
A controlled access layer helps reduce exposure by:
- Encrypting all remote sessions
- Restricting access based on identity and device
- Preventing direct exposure of internal systems to the internet
- Monitoring session behavior for anomalies
This approach limits the attacker’s ability to move freely once inside.
Role of PureVPN White Label VPN Solution
Yurei ransomware highlights a consistent weakness in many organizations: fragmented and poorly controlled remote access. Once attackers gain entry, lateral movement becomes difficult to stop.
The PureVPN White Label VPN Solution addresses this by giving organizations a controlled, branded secure access layer. It enables centralized management of remote connections, ensuring only authenticated users can access internal systems through encrypted channels.
It also helps reduce reliance on exposed services by routing access through secured VPN infrastructure, lowering the attack surface available for credential-based intrusions.
For organizations managing distributed teams or external collaborators, this creates a more consistent security boundary around internal environments.
Closing Perspective
Yurei ransomware reflects a shift in cyberattacks from loud disruption to silent infiltration. It prioritizes time inside systems over immediate damage, turning access itself into the primary weapon.
Once inside, attackers operate quietly, map infrastructure, extract data, and only then activate encryption. By that stage, recovery becomes significantly more complex.
Reducing exposure requires tighter identity control, limited internal movement, and secure remote access channels. The goal is simple: remove the freedom attackers depend on once they enter the network.