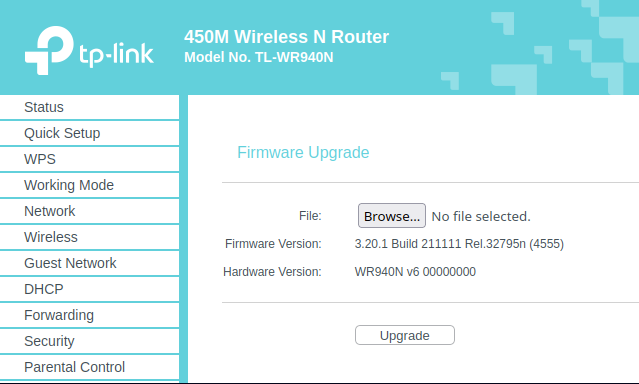
A state-sponsored APT group from China, identified as Camaro Dragon, has been observed exploiting TP-Link routers through a malicious firmware implant.
The discoveries were made by security experts at CheckPoint Research (CPR) and were detailed in an advisory released today.
Modus operandi
“The implant consists of multiple malicious elements, including a customized backdoor named ‘Horse Shell,’ which grants the attackers persistent access, facilitates the establishment of anonymous infrastructure, and enables lateral movement within compromised networks,” stated Itay Cohen, Radoslaw Madej, and the CPR Threat Intelligence Team.
- The implant components are also designed to be compatible with different firmware versions from various vendors.
- The embedded components were identified in modified TP-Link firmware images. However, they were developed in a firmware-agnostic manner and are not exclusive to any particular product or vendor.
- Consequently, they can be incorporated into different firmware by various vendors.
Source: CPR
“While we lack definitive evidence, previous incidents have shown that similar implants and backdoors have been deployed on diverse routers and devices from various vendors.”
- CPR clarified that the method of installing the malicious firmware images on the compromised routers and their actual use in intrusions is still uncertain.
- It is probable that they gained access to these devices by either scanning for known vulnerabilities or targeting devices that utilized default, weak, or easily guessable passwords for authentication.
Facets of attack
Tunneling: By employing numerous tiers of nodes to tunnel communication, malicious actors can obfuscate the source and destination of the traffic, creating challenges for defenders to track the traffic back to the command and control (C2). This increases the complexity for defenders to identify and counteract the attack.
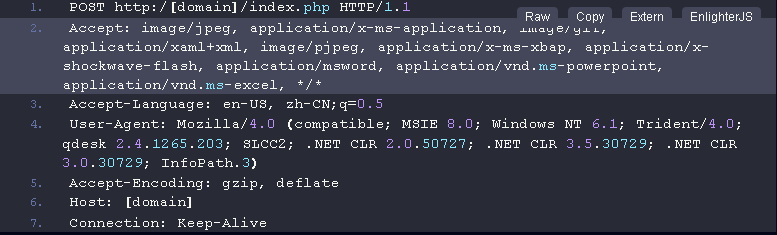
Source: Encrypted message (CPR)
Unused code: The overwhelming majority of the features in the implant are actively utilized. However, a comprehensive analysis has uncovered specific features and submodules that have been disregarded and left unused, akin to a solitary sock misplaced in the laundry.
Although it is plausible that these neglected functionalities are remnants from previous iterations or possibly unrelated to the current variant intended for different devices, their intended use remains an enigma.
Custom crypto: The audacious individuals responsible for Horse Shell have boldly proceeded with a personalized or modified encryption method based on a Substitution-Permutation Network. The implant employs this method to encode and decode the data it sends and receives.
Although this approach falls short of being considered a recommended practice, CPR acknowledges that their examinations have, thus far, yet to uncover any areas for improvement in the implementation.
Extracting what’s learnt
Chinese state-sponsored APT group Camaro Dragon’s assaults on European foreign affairs entities had a deadly firmware implant for TP-Link routers. The implant incorporates a customized backdoor named “Horse Shell,” empowering the attackers to execute actions such as remote shell access, file transfer, and network tunneling, thereby facilitating the anonymisation of their communication through a sequence of compromised nodes.
The research uncovered multiple strategies and tools the Camaro Dragon group employed in their attacks. These findings not only enhance our understanding of the Camaro Dragon group and their toolkit but also contribute valuable knowledge to the broader cybersecurity community, aiding in the comprehension and defense against similar threats in the future.
It is vital to keep your network devices updated and secure and remain vigilant for suspicious activities.