Examining the Linux version of a newly discovered ransomware strain called BlackSuit has revealed significant similarities with another ransomware family called Royal.
Researchers at Trend Micro, who analyzed an x64 VMware ESXi version that targets Linux machines, found an “extremely high degree of similarity” between Royal and BlackSuit.
The two ransomware families are nearly identical, with functions showing 98% similarities, blocks showing 99.5%, and jumps offering 98.9%, as determined by BinDiff, a binary file comparison tool.
- When comparing the Windows artifacts, the similarities were slightly lower but still significant, with functions showing 93.2% similarity, basic blocks showing 99.3% similarity, and jumps showing 98.4% similarity based on BinDiff.
BlackSuit first surfaced in early May 2023, and Palo Alto Networks Unit 42 highlighted its ability to target Windows and Linux hosts.
The knacking ability of BlackSuit
Like other ransomware groups, BlackSuit employs a double extortion scheme that
- steals and encrypts sensitive data from compromised networks and demands monetary compensation.
- The ransomware’s dark web leak site lists the stolen data associated with a single victim.
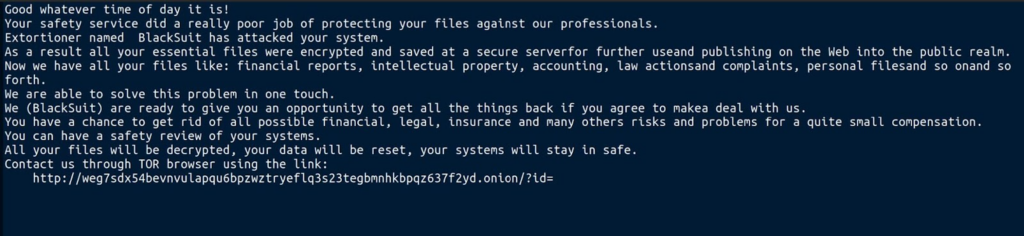
Source: Unit42
Recalling stealth
Trend Micro’s latest findings reveal that both BlackSuit and Royal utilize OpenSSL’s AES for encryption and employ similar intermittent encryption techniques to speed up the process.
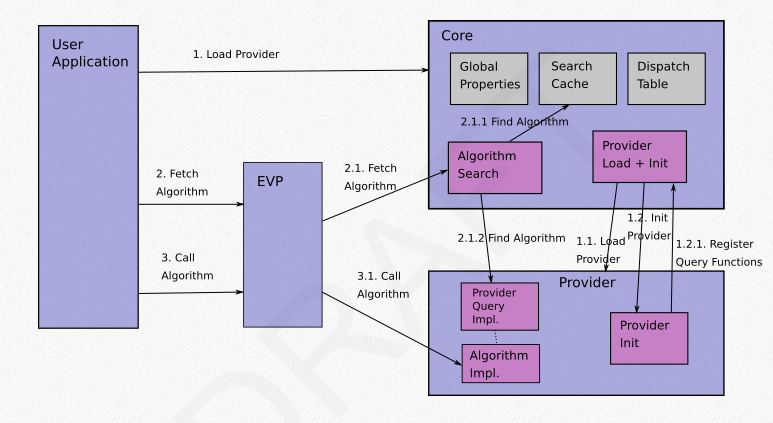
Source: OpenSSL
Despite the similarities, BlackSuit introduces additional command-line arguments and avoids encrypting different files with specific extensions during its operations.
Trend Micro analysis
Trend Micro suggests that the emergence of BlackSuit, resembling Royal, could indicate that it is either a new variant developed by the same authors, a copycat using similar code, or an affiliate of the Royal ransomware gang that has modified the original family.
Given that Royal is a derivative of the former Conti team, it’s also possible that BlackSuit has emerged from a splinter group within the original Royal gang, speculates the cybersecurity company.
These developments again highlight the ever-evolving nature of the ransomware landscape, as new threat actors continually tweak existing tools to generate illicit profits.
Another malware called Wintapix takes the throne in the Middle East, attacking Windows. An unidentified cyber threat actor has been detected employing a malicious Windows kernel driver in attacks that appear to be targeting the Middle East since at least May 2020.
Sight ahead
The rise of BlackSuit ransomware (with its resemblances to Royal) suggests that it could be either a new variant crafted by the same authors, a mimic using similar code, or an associate of the Royal ransomware gang that has introduced alterations to the original lineage.
One plausible scenario behind the birth of BlackSuit is that the notoriety of the Royal group (and its predecessor, Conti) as one of the most active ransomware factions today might have attracted the attention of other cybercriminals, who then took inspiration to fashion BlackSuit as a comparable ransomware strain.
Another possibility is that BlackSuit emerged from a splinter faction within the original Royal gang.
Regardless of the origin, the arrival of yet another ransomware like BlackSuit reinforces the notion that threat actors are ceaselessly searching for more potent attack tools.
They adapt existing code or forge distinct ransomware families to exploit their victims and maximize gains. Hence, organizations and individuals must maintain constant vigilance in safeguarding their files and data from ransomware attacks.









