Credential stuffing has evolved into a board-level security risk. Attackers no longer need sophisticated exploits; they simply log in using stolen passwords. And unfortunately, it works.
Billions of exposed credentials are circulating on the dark web, while password reuse remains widespread across both consumers and employees.
For enterprises managing thousands of identities across SaaS apps, cloud platforms, and remote work environments, the attack surface has exploded. The result is account takeovers, data breaches, and costly incident response cycles.
Organizations that combine strong password hygiene with enterprise password managers can reduce credential stuffing risk. In the guide, you’ll learn why password reuse is still the biggest weakness and how password managers mitigate attacks at scale.
What Is Credential Stuffing?
Credential stuffing is an automated cyberattack where attackers use previously leaked usernames and passwords to attempt logins across multiple services. How the attack works:
- Attackers obtain credential dumps from breaches or infostealer malware
- Bots attempt mass logins across websites and enterprise portals
- Reused passwords allow attackers to gain access
- Compromised accounts are monetized or used for lateral movement
Unlike brute force attacks, credential stuffing uses valid credentials, making detection harder.
Why it works so well?
That’s simply because users still reuse passwords everywhere.
- 70% of exposed users reused compromised passwords across accounts.
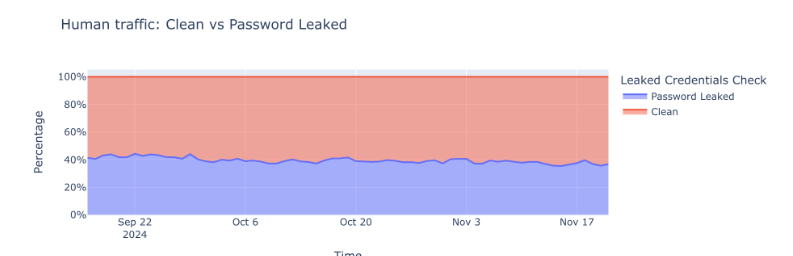
- Nearly 41% of successful logins involve leaked credentials.
- Over 193 billion credential stuffing attempts were recorded in one year.
For enterprises, this creates a perfect storm.
Latest Credential Stuffing Breaches You Must be Aware Of
Credential stuffing isn’t theoretical, it’s actively causing major incidents.
Roku Account Takeover Wave
In 2024, Roku disclosed that attackers accessed roughly 576,000 user accounts using credentials stolen from other sites. The company confirmed this was a credential stuffing attack and forced password resets plus mandatory MFA.
Key lesson for enterprises: Your systems can be secure and still be compromised through reused passwords.
Massive Credential Exposure Datasets
Security researchers uncovered datasets containing around 16 billion login records, largely harvested by infostealer malware. Even when not tied to a single breach, these datasets fuel credential stuffing campaigns for years.
Email Password Mega-Leak
Another incident exposed 183 million email passwords, many appearing in breaches for the first time. Experts warned attackers would likely weaponize the data through credential stuffing.
Surge in Credential Theft
Credential theft rose 160% in 2025, now contributing to roughly one in five breaches. Attackers increasingly use AI-driven automation to scale attacks.
Why Enterprises Are Vulnerable To Credential Stuffing Attacks
Modern enterprises unintentionally amplify credential risk.
1. Identity Sprawl
Organizations now manage:
- SaaS applications
- Cloud consoles
- Remote access portals
- Developer tools
- Partner integrations
Each new login is another potential entry point.
2. Password Reuse Among Employees
Despite training, employees still reuse passwords between:
- Personal accounts
- Corporate apps
- Third-party services
One breach outside your organization can compromise internal systems.
3. Human Behavior Remains the Weak Link
Credential-based attacks account for a significant share of breaches. In fact, stolen credentials initiated 22% of breaches, the highest of any vector.
4. AI is Accelerating Attacks
New AI agents are making credential stuffing cheaper and more scalable, allowing attackers to automate web interactions at low cost.
The Business Impact of Credential Stuffing
Credential stuffing is not just an IT problem; it’s a financial and reputational risk.
Direct Financial Damage
Credential-based attacks can cause significant direct financial damage to organizations. On average, a breach involving stolen or reused credentials costs around $4.81 million, making it one of the most expensive security incidents to remediate.
What makes these attacks especially dangerous is their ability to remain undetected for months, quietly expanding the blast radius. During this time, fraud, account takeovers, and unauthorized purchases continue to pile up, ultimately increasing customer support workloads, reimbursement costs, and overall incident response spending.
Operational Consequences
Beyond financial losses, credential attacks can severely disrupt day-to-day operations. Organizations often experience account lockout storms that overwhelm authentication systems and frustrate legitimate users.
Helpdesk tickets surge as employees and customers struggle to regain access, stretching IT support teams thin. At the same time, repeated account issues can drive customer churn, while ongoing security incidents increase regulatory scrutiny and compliance risk. Over time, the cumulative effect leads to measurable erosion of brand trust and user confidence.
Security Team Burnout
Credential-based attacks flood authentication logs with massive volumes of noise, making it difficult for SOC teams to quickly separate real threats from routine anomalies. As analysts chase false positives and investigate repeated login abuse, alert fatigue sets in, response times slow, and critical indicators of compromise can be missed.
Over time, this constant pressure contributes to security team burnout, reduced operational efficiency, and increased risk exposure.
How Enterprise Password Managers Mitigate Credential Stuffing
Password managers are one of the most effective and underutilized tools. They help to:
- Enforcing strong, unique passwords
Password managers automatically generate high-entropy passwords for every account.
Security benefit:
If one credential leaks, it cannot be reused elsewhere. This directly breaks the credential stuffing kill chain.
2. Eliminating Password Reuse at Scale
Enterprise vaults give security teams visibility into weak or reused passwords. They enable:
- Password health dashboards
- Reuse detection
- Policy enforcement
- Automated resets
This turns password hygiene from a hope into a measurable control.
3. Supporting Phishing-Resistant Authentication
Modern password managers integrate with:
- MFA
- Passkeys
- Hardware keys
- SSO platforms
Together, these create layered identity protection.
4. Reducing Shadow IT Credential Risks
Employees often store passwords in:
- Browsers
- Spreadsheets
- Sticky notes
- Personal vaults
Enterprise password managers centralize and secure credentials, reducing leakage risk.
5. Improving Incident Response
When a breach occurs, password managers allow:
- Rapid credential rotation
- Forced resets
- Access audits
- Compromised password detection
This can effectively reduce attacker dwell time.
What Should Enterprises Do to Stop Credential Stuffing
Stopping credential stuffing requires a coordinated strategy that combines strong password hygiene, intelligent authentication, continuous monitoring, and user awareness. Below are the most effective steps enterprises should take now to reduce account-takeover risk and harden their identity perimeter.
Enforce Unique Passwords Everywhere
Every account should have a strong, unique password. At a minimum, require:
- 14+ character length
- Random, high-entropy generation
- Zero password reuse across systems
Manually enforcing this at scale is nearly impossible. An enterprise-grade solution like PureVPN Password Manager simplifies the process by automatically generating complex passwords, securely storing them in an encrypted vault, and giving administrators visibility into password health across teams.
Deploy MFA, But Don’t Rely on it Alone
Multi-factor authentication is essential, but it shouldn’t be your only line of defense. Modern attackers increasingly target MFA workflows through fatigue attacks and phishing proxies. Prioritize phishing-resistant methods such as:
- Authenticator apps
- Hardware security keys
- Passkeys
Avoid SMS where possible due to SIM-swap risks. When paired with a password manager that promotes strong credential hygiene, MFA becomes far more effective because attackers are less likely to obtain valid passwords in the first place.
Monitor for Credential Exposure
Security teams need continuous visibility into whether employee credentials have been exposed outside the organization. Monitoring should include:
- Dark web leak detection
- Infostealer log tracking
- Breach notification feeds
Advanced enterprise password managers help reduce response time by flagging weak, reused, or compromised credentials, allowing teams to trigger rapid password resets before attackers act.
Implement Bot and Login Protections
Because credential stuffing is fundamentally an automation problem, technical controls must disrupt bots at scale. Key protections include:
- Rate limiting
- CAPTCHA challenges
- Device fingerprinting
- Behavioral analytics
These controls reduce attack volume, while strong password hygiene ensures that even successful login attempts rarely succeed.
Train Employees on Password Hygiene
Technology alone isn’t enough. Human behavior still plays a major role in credential risk. Security awareness programs should reinforce:
- Never reuse passwords
- Always use the enterprise password vault
- Recognize phishing attempts
- Report suspicious login alerts immediately
When employees consistently use a secure vault like PureVPN Password Manager, organizations gain both stronger credentials and better visibility.
Frequently Asked Questions
Credential stuffing uses real leaked passwords, while brute force guesses passwords. Stuffing is more dangerous because it often bypasses lockout controls.
MFA significantly reduces risk but is not foolproof. Attackers can still exploit MFA fatigue, phishing proxies, and session hijacking. It is a good idea to combine MFA with password managers and behavioral detection.
Yes, when properly implemented. Enterprise password managers use strong encryption and access controls that are far safer than manual password handling.
Common sources include data breaches, infostealer malware, phishing, credential marketplaces, and password reuse across sites.
High-risk sectors include retail and e-commerce, financial services, SaaS platforms, education , and healthcare. These sectors see heavy automated login traffic.
Wrap Up
Credential stuffing has become one of the most predictable and preventable causes of enterprise breaches. The threat is accelerating in recent times. Enterprises that still rely on employee memory, browser storage, or weak password policies are leaving the front door unlocked.
A modern enterprise password manager changes the equation by eliminating password reuse, enforcing strong credentials, enabling rapid response and supporting layered authentication. When combined with MFA, monitoring, and user education, it becomes one of the most cost-effective ways to mitigate credential stuffing risk.








