Modern IT environments are expanding faster than most security teams can track. Between cloud workloads, IoT devices, remote endpoints, and shadow IT, organizations often struggle to maintain a reliable asset inventory. That’s where agentless asset discovery comes in.
Instead of installing software on every device, agentless discovery identifies assets across your environment using network-based techniques and APIs. The result is faster visibility, lower overhead, and broader coverage.
In this comprehensive guide, you’ll learn what agentless asset discovery is, how it works, key benefits and limitations, and more.
What Is Agentless Asset Discovery?
Agentless asset discovery is the process of identifying and cataloging devices, systems, and digital assets across IT environments without installing software agents on each endpoint. Instead of relying on local software, agentless tools gather information through:
- Network traffic analysis
- API integrations
- Remote protocols (like SNMP, WMI, SSH)
- Deep packet inspection
By listening to communications across the network, these tools can detect device types, IP addresses, operating systems, and sometimes software details. In simple terms: agentless discovery sees your assets from the outside in.
Why Asset Discovery Matters in Modern Cybersecurity
Organizations today face:
- Rapid cloud expansion
- Remote and hybrid work
- Exploding IoT/OT devices
- Shadow IT proliferation
Enterprises are deploying new assets at unprecedented rates, making it difficult for security teams to track and secure the growing attack surface. Without continuous asset visibility, organizations risk:
- Unknown attack paths
- Compliance failures
- Vulnerability blind spots
- Incident response delays
Agentless discovery directly addresses this visibility gap.
How Agentless Asset Discovery Works
Agentless discovery operates using three primary methods.
1. Passive Network Monitoring
The tool monitors network traffic and analyzes communication patterns between devices. Using techniques like deep packet inspection (DPI), it can identify:
- Device make and model
- Operating system
- Software versions
- Communication behavior
This works without touching the endpoint itself.
Best for: IoT, OT, unmanaged devices.
2. Active Network Queries
Some agentless tools perform authenticated scans using standard protocols such as:
- SNMP
- WMI
- SSH
- Remote PowerShell
These queries pull asset data remotely without installing software locally.
Best for: Servers, workstations, network devices.
3. API-Based Cloud Discovery
In cloud environments, agentless tools connect directly to provider APIs. This enables visibility into:
- Virtual machines
- Containers
- Serverless workloads
- Storage resources
Because cloud resources can be short-lived, API-based discovery scales naturally with dynamic environments.
Best for: AWS, Azure, GCP environments.
Key Benefits of Agentless Asset Discovery
As IT environments grow more complex and distributed, organizations are under pressure to gain full asset visibility, without adding operational friction. By eliminating the need to deploy and maintain endpoint agents, it offers a faster, lighter, and more scalable way to uncover assets across modern networks. Here’s why security and IT teams are increasingly turning to it.
Faster Deployment
No endpoint installation means teams can deploy quickly across large environments. Many solutions begin scanning immediately after setup.
Impact: Faster time-to-value.
Lower Operational Overhead
Since there are no agents to maintain:
- No patching per endpoint
- No compatibility headaches
- No endpoint performance impact
Maintenance happens centrally on the discovery server.
Impact: Reduced IT workload.
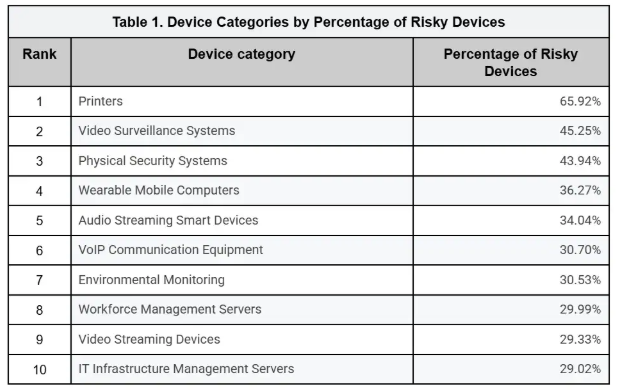
Broader Asset Coverage
Agentless discovery excels at finding devices that cannot support agents, including:
- Printers
- Routers
- IoT devices
- OT systems
This makes it valuable in modern heterogeneous environments.
Minimal Endpoint Performance Impact
Because no software runs locally, agentless methods avoid consuming CPU or RAM on endpoints.
Impact: Better user experience.
Strong Scalability for Cloud Environments
Agentless tools can automatically detect new cloud resources through API integrations, making them ideal for elastic infrastructure.
Impact: Cloud-native visibility.
Improved Security Visibility
Continuous monitoring helps organizations:
- Identify shadow IT
- Detect unauthorized devices
- Prioritize vulnerabilities
- Support compliance audits
Up-to-date asset inventories significantly reduce security blind spots.
Limitations of Agentless Asset Discovery
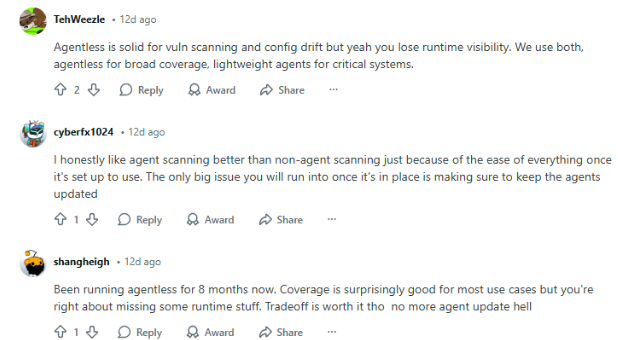
While agentless asset discovery delivers speed, scalability, and broad visibility, it isn’t a one-size-fits-all solution. Like any security approach, it comes with trade-offs that organizations need to understand before relying on it exclusively.
- Dependence on Network Connectivity
Agentless discovery works by observing network activity, so its effectiveness depends heavily on what it can see. If a device isn’t communicating on the network—or is hidden behind tight controls, it may slip under the radar.
Devices most likely to be missed include:
- Offline systems
- Remote endpoints outside network visibility
- Assets behind restrictive firewalls or segmented networks
This is why many organizations pair agentless methods with complementary visibility controls to reduce blind spots.
- Less Granular Endpoint Insight
Agentless discovery is excellent for broad visibility, but when it comes to deep, host-level intelligence, it can fall short compared to agent-based approaches. Because there’s no software running directly on the endpoint, agentless methods may struggle to capture:
- Real-time application usage
- Deep host telemetry
- Memory-level or kernel activity
This limitation matters in high-security environments. Agents can continuously stream behavioral data, file integrity changes, and process activity, while agentless tools typically rely on periodic scans or API snapshots.
As a result, certain use cases, like advanced threat detection, detailed compliance auditing, or runtime attack visibility, may require agent-based telemetry for full coverage.
- Potential Network Overhead
Because agentless discovery relies on network scans and remote queries, aggressive or poorly tuned polling can introduce additional traffic across the environment. In large or highly distributed networks, frequent scanning may consume noticeable bandwidth and, in some cases, impact the performance of sensitive systems.
This risk is usually manageable with proper configuration, but organizations should be mindful when:
- Scanning large IP ranges
- Running frequent active queries
- Monitoring bandwidth-constrained or latency-sensitive networks
Best practice: tune scan frequency, use scheduling during low-traffic windows, and combine passive monitoring where possible to minimize network strain while maintaining strong visibility.
- Credential Management Risks
Agentless asset discovery often requires storing privileged credentials centrally, which can create a high-value target if not properly secured. Industry data shows stolen credentials remain one of the leading causes of breaches, enabling lateral movement and privilege escalation.
Scanners can become keys to the kingdom when over-privileged. To stay safe, organizations should enforce least privilege, use credential vaults, and rotate access regularly.
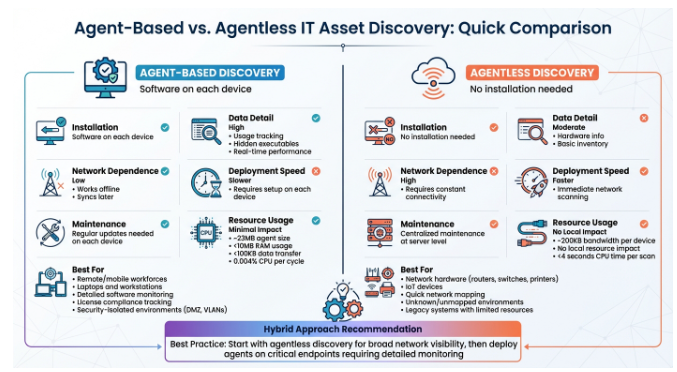
Agentless vs. Agent-Based Asset
| Agentless Discovery | Agent-Based Discovery | |
| Pros | – No endpoint installation- Quick deployment- Broad device coverage- Minimal endpoint impact- Scales well in cloud | – Deep endpoint visibility- Works offline- Real-time monitoring- Detailed software inventory |
| Cons | – Less granular telemetry- Network dependent- May miss offline assets | – High deployment effort- Ongoing maintenance- Endpoint performance impact- Slower scalability |
Why Do Most Organizations Use a Hybrid Approach?
Mature security programs don’t rely solely on agentless or agent-based discovery; they use a hybrid strategy. Agentless methods provide rapid, broad visibility across networks and cloud environments, while agent-based tools deliver deep, real-time telemetry on endpoints.
Research from Gartner and industry surveys shows that organizations combining both approaches achieve the best balance between coverage and depth, reducing blind spots while maintaining detailed insights for compliance and threat detection.
Industrial and IoT devices, such as smart sensors, cameras, or HVAC systems, often cannot support agent installation due to hardware or OS limitations. Agentless monitoring solves this challenge by identifying these devices through network traffic and protocol analysis.
According to a 2025 IoT security report by Palo Alto Networks, over 70% of industrial IoT devices in enterprise environments remain unmanaged, creating significant blind spots, agentless discovery helps close that gap without disrupting operations.
Cloud environments are dynamic: virtual machines, containers, and serverless functions appear and disappear constantly. Agentless discovery tools integrate with cloud provider APIs to track ephemeral assets in real time, ensuring teams have up-to-date inventories.
This capability is critical for cloud-native security frameworks and reduces the risk of forgotten workloads being exposed to the internet. Research by Forrester emphasizes that automated cloud asset mapping significantly lowers misconfiguration risks and improves incident response times.
Shadow IT, unauthorized SaaS usage, rogue devices, or forgotten servers, poses a hidden risk to enterprises. Agentless tools can detect these unmanaged assets by monitoring network behavior and API access patterns, providing security teams with visibility they might otherwise lack.
A survey from Gartner found that over 50% of organizations had at least one major shadow IT incident in the past year, highlighting the importance of continuous agentless monitoring.
During M&A activity, organizations often inherit unknown IT environments. Agentless discovery enables rapid mapping of all devices and systems without installing agents, helping IT and security teams perform due diligence efficiently.
A report from Accenture shows that lack of visibility during acquisitions is a leading cause of post-merger breaches, agentless discovery can prevent costly oversights.
Maintaining an accurate and comprehensive asset inventory is critical for compliance with standards like ISO 27001, NIST, PCI DSS, and HIPAA. Agentless discovery tools continuously update inventories and produce audit-ready reports, ensuring organizations can demonstrate adherence to regulatory requirements.
According to ISACA’s 2025 IT Audit survey, organizations leveraging continuous discovery reduced audit preparation time by up to 40% while improving control effectiveness.
Agentless discovery excels in areas that agents cannot reach, IoT, cloud, shadow IT, and transitional environments like mergers, making it an irreplaceable part of a comprehensive asset management strategy.
Best Practices for Implementing Agentless Asset Discovery
To get the most value, follow these proven strategies.
- Combine Passive and Active Methods – Use multiple discovery techniques to avoid blind spots and achieve full coverage.
- Secure Administrative Credentials – Protect privileged access with vaulting, least privilege, and regular rotation.
- Integrate With Your Security Stack – Feed discovery data into SIEM, CMDB, vulnerability scanners, and EDR/XDR for actionable insights.
- Monitor Continuously – Run ongoing discovery instead of point-in-time scans to catch new assets promptly.
- Consider a Hybrid Strategy – Combine agentless methods for breadth and agents for deep endpoint visibility.
The Future of Agentless Asset Discovery
The trend is clear: environments are becoming more dynamic and distributed. Agentless discovery is evolving with:
- AI-driven asset classification
- Real-time attack surface mapping
- Cloud-native integrations
- Identity-aware asset context
As organizations adopt zero trust and continuous exposure management, agentless visibility will become even more critical.
Wrap Up
Agentless asset discovery has become a foundational capability for modern cybersecurity programs. By eliminating the need for endpoint agents, it delivers rapid deployment, broad coverage, and scalable visibility across increasingly complex environments.
However, network dependence and limited host depth mean the smartest organizations treat agentless discovery as one critical layer in a broader visibility strategy. If your goal is to reduce blind spots, uncover shadow IT, and understand your true attack surface, agentless discovery is what you need now.
Frequently Asked Questions
Its primary goal is to automatically identify and inventory all devices and digital assets across an environment without installing software agents, improving visibility and reducing blind spots.
Yes, when properly configured. However, organizations must secure stored credentials and ensure network access controls are tightly managed.
It depends. Devices that are offline or outside network visibility may be missed, which is why many teams adopt a hybrid approach.
Neither is universally better. Agentless offers broad, fast visibility, while agent-based provides deeper endpoint telemetry. Most enterprises use both.
Yes. Modern tools integrate directly with cloud provider APIs, allowing them to detect short-lived workloads and dynamic infrastructure.