Table of Contents
Every year in October, PureVPN collaborates with Stay Safe Online to support its cybersecurity agenda. The primary purpose of this month is to emphasize the importance of online privacy and security in today’s surveillance era.
PureVPN advocates for online privacy; hence, anonymity is dear to us. We strongly value events that create public awareness about online threats and educate internet users to use a VPN to stay secure online.
Identity theft is becoming increasingly prevalent with every passing year. Even if you haven’t yet been affected by the crime, realizing that your personally identifiable information (PII) is precious to cyber thieves is essential.
A stolen identity can have awful consequences, and clearing up the resulting mess may take weeks, or worse, even months! In this article, we’ll discuss what identity theft is all about and how you can take your identity theft protection up a notch to keep this from ever happening to you.
What is identity theft – A definition
Identity theft, also known as identity fraud, occurs when an imposter steals your personal information, like name, date of birth, phone number, and Social Security Number, to commit fraud or obtain financial benefits.
They might steal money from your bank accounts, take out credit in your name, set up fake online accounts, or make unauthorized purchases by projecting a fraudulent identity. It can happen to anyone if they aren’t careful enough, so guarding your information closely is crucial.
5 signs that someone has stolen your identity
You may wonder, “How can I even tell if my identity has been stolen?” Well, there’s no definite answer to that question. After all, there are a myriad of signs which may indicate that your identity is compromised. Regardless, the following are some of it’s clues:
- You’re not receiving statements, bills, and other mail.
- You’re denied credit or offered unfavorable terms.
- You’re getting invoices or notices for purchases you haven’t made.
- You’re noticing unauthorized transactions on your bank or credit card account.
- You’re being rejected for legitimate medical claims because of reaching your benefits limit.
Types of identity theft
Many kinds of identity theft can occur, so that anyone can become a victim. As such, the more you know about them, the better you’ll be able to protect yourself. Below, we have discussed it’s most common types that you could encounter:
Medical ID theft
A type of insurance fraud that involves individuals acquiring medical services or prescriptions using someone else’s name. As a result, the impostor’s medical information would be added to the medical records of the victim, exposing them to financial losses due to insurance costs and medical bills.
Source: Reddit
Social Security ID theft
A thief uses your Social Security Number, the most important number any American possesses, to steal money and property or access services and opportunities solely available to social security holders. They may even use your SSN to forge fake documents such as passports.
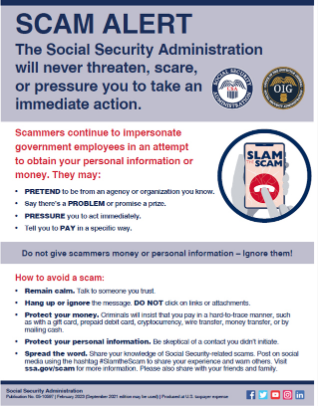
Source: www.ssa.gov
Financial ID theft
As the name implies, this occurs when a victim’s bank account or credit card details are stolen and used for purchasing goods and services. The offender could even use that information to access new financial services or credit cards, resulting in considerable loss of money and ruining your financial security.
Contact the identity theft resource center.
Driver’s license ID theft
One of the most common forms of identity theft is a perpetrator stealing your driver’s license, which provides details like your name, address, date of birth, and Social Security Number. This information is used to purchase items, apply for loans, open new bank accounts, etc., under your name.
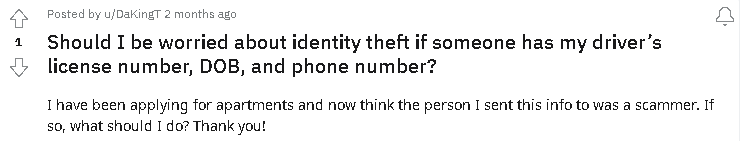
Source: Negligent Reddit user
Child ID theft
Though this type may not be as common as the others, it’s highly lucrative for thieves. Children’s Social Security Numbers are valuable as there’s usually no information linked to them, so criminals can easily use them to commit fraud.
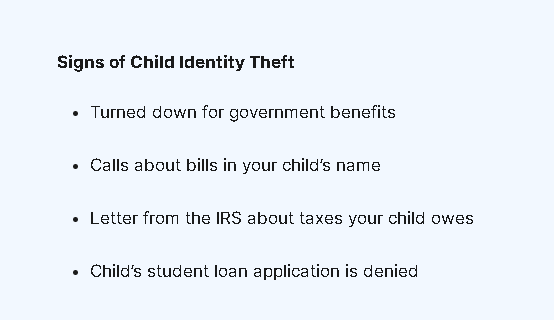
Source: FTC
Identity theft examples
Now that you know what identity theft is, the signs that indicate that you may have been a victim, and which are the most common types, let’s take a closer look at a few examples:
- Someone uses your Social Security Number to rent cars and commit crimes.
- Someone uses your personal information to open new accounts in your name.
- Someone uses your credit card or debit card to make unauthorized purchases.
- Someone uses your child’s identity to take out loans and other lines of credit.
- Someone uses your health insurance details for medical care.
Identity theft laws
We reached out to Glenn Kurtzrock, a criminal defense attorney in Long Island, NY, and asked him a few questions regarding identity theft laws:
Is identity theft a misdemeanor or a felony?
GK: “In New York State, there are four degrees of Identity Theft. There is Identity Theft in the First Degree, through the Third Degree, and Aggravated Identity Theft.
To summarize them from least severe to most serious, ID Theft in the Third Degree is a class A misdemeanor. It involves knowingly and with intent to defraud, assuming the identity of another person, and thereby benefiting from doing that or causing harm to the other person.
ID Theft in the Second Degree is a class E felony. It involves committing the crime of ID Theft in the Third Degree and either benefitting in an amount over $500, harming the other person above $500, committing or attempting to commit another felony, or having a prior conviction for ID Theft in the Third Degree or a related crime in the previous five years.
ID Theft in the Third Degree is a class D felony. It involves committing the crime and either benefiting in an amount over $2,000, harming the other person over $2,000, committing or attempting to commit a class D or higher felony, or having a prior conviction for ID Theft in the Second Degree or a related crime in the previous five years.
Aggravated ID Theft is also a class D felony. It involves knowingly and intending to defraud, assuming the identity of a member of the armed forces deployed outside of the US, and either benefitting over $500 or harming the other person over $500.
It’s important to note that several other crimes are usually charged in connection with Identity Theft charges, which overlap with these charges. I often see additional expenses including but not limited to Criminal Impersonation, Forgery, Criminal Possession of a Forged Instrument, and more.”
How long is jail time for Identity Theft?
GK: ” It will vary depending on how the offense is charged:
- A misdemeanor – up to 1 year in jail
- E felony – up to 1 1/3 to 4 years in prison
- D felony – up to 2 1/3 to 7 years in jail “
Should I file a police report for identity theft?
GK: “That’s up to you, but many of these cases can involve ancillary consequences such as issues with your credit report or identification, so it’s helpful to show that you reported this to the police.”
What is the bail amount for identity theft?
GK: “That varies widely depending on many factors, including the level of the offense, the prior criminal history of the defendant (or lack thereof), the nature of the crime, the harm to the victim, the strength of the prosecution’s case, and the likelihood that the defendant will attempt to flee the jurisdiction. Sometimes, it’s possible to negotiate with the prosecutor before the arraignment to agree on bail.
For example, I recently had a client arrested and charged with several counts of Identity Theft and related crimes. The prosecutor was going to ask for $20,000 bail to be set. Before the arraignment, I obtained documentation demonstrating that this was my client’s real identity.
The prosecutor agreed to consent to my client being released without bail. I then obtained and provided several additional documents proving that my client was innocent of the charges, and the prosecutor agreed to dismiss all costs.”
How to protect your identity
While it can prove challenging to prevent becoming its victim entirely, there are specific steps that you can take to minimize the risk of your identity getting stolen. Here’s how you can do just that:
1. Be wary of Public WiFi networks
If you connect to free WiFi without protection, hackers can sniff your traffic and steal personal information. A VPN allows you to change your IP address to surf anonymously, allowing you to use public WiFi without worrying about someone monitoring your every move.
2. Enable two-factor authentication
Two-factor authentication, also called 2FA, will add an extra layer of security to your online and financial accounts. Therefore, make sure to set it up wherever possible. You’ll be asked to confirm your identity every time you attempt to log in by scanning a QR code or entering a unique code.
3. Use a password manager
Many security experts recommend using strong, unique passwords, but remembering multiple credentials can be inconvenient. A reliable password manager will not only generate strong passwords for you and help keep them secure under one master password.
4. Lock down your social media
Identity thieves might learn a lot about you by looking at the information you post on social media platforms like Instagram, Facebook, and Twitter. Make sure you don’t share personally identifiable information with them. Also, become familiar with and use the various privacy settings available.
5. Exercise caution when giving out personal info
One way criminals can get their hands on your information is through phishing. They pose as a legitimate institution to lure individuals into revealing their passwords, credit card details, and other information. Remember, if your institution contacts you, they already have your info.
6. Never click on suspicious links
If you receive a dubious link, trust your gut and delete it immediately. Better to be safe than sorry. Similarly, if you get a phone call from someone claiming to be your credit card company, hang up and call them back on their official number to confirm if the caller is authentic. Genuine.
7. Set up account alerts
Scammers usually take the first test with a small credit card purchase to check whether it works. Therefore, you should pay close attention to any charges on your accounts. Consider setting up a real-time app or email alert, as you get notified every time there has been a transaction.
8. Only visit “HTTPS” websites
When banking or shopping online, only visit sites that use SSL/TLS encryption to secure your personal information from prying eyes. Using a privacy extension like HTTPS Everywhere, you can enforce HTTPS on all pages.
How does identity theft work?
Though it’s one of the fastest-growing cyber crimes in the U.S., Many people don’t know the first thing about identity theft. Not anymore, though, as we’re going to take a closer look at how it works for your better understanding:
Step #1: Obtaining personal data
The first and most obvious step in identity theft is when thieves steal your data. They can do this in many ways, such as malware, phishing, man-in-the-middle, physical theft, and data breaches.
However, the fact that your credit card details or Social Security number fell into the wrong hands doesn’t constitute identity theft. Your data is merely stolen; the thieves haven’t used it to their advantage.
Step #2: Using the stolen identity
This is when the actual identity theft takes place—the bad guys start using the information they managed to collect on you. They will often also test the authenticity of the stolen data.
If it proves accurate, they will either try to steal more information from you or immediately use the data available. They can use your data in various ways, such as taking out loans or committing insurance fraud.
Step #3: Discovery & correction
Some kinds of identity theft, like the misuse of debit or credit cards, can be identified immediately. However, many forms of fraud, such as child identity theft, remain undiscovered for months or even years.
Identity thieves can also use someone’s insurance information to acquire health care services. The victims don’t know about this unless they seek medical attention and are denied owing to non-payment of past due balances. If you’re a victim, these delays are bad news because the longer it takes to spot identity theft, the more significant the damage caused by the perpetrators.
Identity theft correction can be a hassle and rather lengthy. Depending on how long your stolen identity went undetected, it could take thousands of hours to resolve the issues caused by it.
How to report identity theft to the Police
If you’re a victim of identity theft, it’s recommended that you file an FTC Identity Theft Report first and include it when filing a police report. Follow these steps when reporting identity theft to the police.
- Visit your local police department with these critical pieces of information: a copy of your Identity Theft Report with the Federal Trade Commission (FTC), a copy of your driver’s license or other government-issued photo identification card (ID), proof of your home address, such as a utilities bill or mortgage statement, and any evidence of your stolen identity, such as collection notices or credit card statements.
- Tell the police that a thief has stolen your identity, and you want to file a report. Make sure they attach your FTC complaint to the police report.
- Obtain a copy of the report. You must provide documents to credit bureaus and creditors as you take the necessary steps for identity recovery.
How important is identity theft protection?
Identity theft protection companies claim to guard your personal information in exchange for a specific fee. They generally provide credit monitoring and other services to alert you in case of a problem.
However, most don’t prevent thieves from misusing or stealing your data. We recommend opting for an identity theft protection service only if it offers proactive credit freezes to stop fraudulent account openings.
Identity theft insurance plan: Is it worth it?
Whether identity theft insurance is worth it depends on various factors and personal circumstances. Here are some points to consider when evaluating its value.
Coverage: Identity theft insurance typically covers expenses related to identity theft, such as legal fees, credit monitoring services, and lost wages. Review the policy details to understand the specific costs and coverage limits provided.
LifeLock is a prominent provider of identity theft protection services. They offer various plans that include features like credit monitoring, identity theft alerts, lost wallet protection, and reimbursement for certain expenses related to identity theft.
Risk assessment: Consider your personal risk level for identity theft. Factors like the nature of your work, your online presence, and the security measures you have in place can influence your vulnerability. Insurance may offer more value if you believe you are at a higher risk.
IdentityForce is another reputable company specializing in identity theft protection. It offers comprehensive plans that include credit monitoring, social media monitoring, identity restoration assistance, and insurance coverage for certain related expenses.
Existing protections: Assess your existing protections, such as credit monitoring services, fraud alerts, and strong security practices. If you already have robust safeguards, the additional coverage provided by identity theft insurance may be redundant.
Experian, one of the major credit reporting agencies, offers identity theft protection services that include credit monitoring, dark web surveillance, identity restoration assistance, and insurance coverage for certain costs associated with identity theft.
Financial impact: Consider the potential economic consequences of identity theft. Evaluate the likely costs of resolving the issue, such as legal fees, credit monitoring subscriptions, and any potential loss of income. Compare these potential expenses to the price of the insurance premiums.
Peace of mind: For some individuals, the peace of mind provided by identity theft insurance is valuable. Knowing that you have additional protection and support in case of identity theft can give you a sense of security.
Allstate, known for its insurance products, provides identity theft insurance as an optional add-on to their homeowner’s or renter’s insurance policies. This coverage can include reimbursement for legal fees, lost wages, and document replacement.
Alternative options: Instead of purchasing identity theft insurance, you may opt for free or low-cost measures to protect your identity, such as monitoring your credit reports regularly, setting up fraud alerts, and practicing online solid security habits.
Zander Insurance offers identity theft protection plans that include credit monitoring, identity theft recovery services, and reimbursement for certain expenses incurred due to identity theft.
Ultimately, the decision to purchase identity theft insurance should be based on a thorough evaluation of your circumstances, risk level, and financial considerations. Before deciding, it can be helpful to compare different insurance policies, understand the coverage offered, and assess the cost-benefit ratio.
Identity theft management: Latest trends
Biometric authentication: As traditional forms of authentication (such as passwords) become increasingly vulnerable to theft, biometric authentication methods have gained popularity. Techniques like fingerprint scanning, facial recognition, and iris scanning offer more secure means of verifying identity.
Artificial Intelligence (AI) and Machine Learning (ML): AI and ML technologies are being used to detect and prevent identity theft. These systems analyze patterns, detect anomalies, and flag suspicious activities in real-time, allowing organizations to take prompt action.
Multi Factor Authentication (MFA): Multi Factor authentication combines multiple verification methods to enhance security. It typically requires users to provide two or more forms of identification, such as a password, a fingerprint scan, or a one-time passcode sent to a mobile device.
Identity monitoring services: Security monitoring services constantly monitor individuals’ personal information across various platforms and alert them to suspicious activities or breaches. These services can help individuals respond quickly to potential identity theft attempts.
Behavioral analytics: Analyzing user behavior and patterns can help identify anomalies and potentially fraudulent activities. Organizations can detect unusual activities and take appropriate action by tracking how users interact with systems and comparing it to current behavior.
Dark web monitoring: The dark web is a haven for cybercriminals trading stolen personal information. Identity theft management services now offer dark web monitoring, which involves scanning the dark web for individuals’ data to identify any compromised information proactively.
Internet of Things (IoT) Security: As IoT devices become more prevalent, securing these interconnected devices is critical to prevent identity theft. Weak security measures on smart home devices, wearables, and other IoT devices can allow hackers to access personal information.
Passwordless authentication: Passwords are often vulnerable to theft or hacking. Passwordless authentication methods, such as using biometrics, hardware tokens, or secure authentication apps, eliminate the need for traditional passwords and enhance security.
youtu.be/QmWVmMFVF0Q #AVDConfig
Blockchain technology: Blockchain offers a decentralized and tamper-resistant system for storing and verifying data. It has the potential to enhance identity management by providing a secure and transparent framework that minimizes it’s risk.
Keep safe what belongs to you only
If you discover that your identity is stolen, you must report the crime immediately to the relevant agencies. It will allow you to clear up any fraud using your name and personally identifiable information before it negatively affects you and your finances.
Frequently Asked Questions
These are some ways to prevent it.
– Freeze your credit
– Safeguard your Social Security number
– Be alert to phishing
– Use strong passwords and add an authentication step
– Use alerts
– Watch your mails
– Use a digital wallet
– Be vigilant
Yes, identity theft is a crime. Stealing someone’s confidential information and using it for their own purpose is a crime.
Yes, identity theft can be controlled through MFA, blockchain security, and many more techniques.
The goal is usually financial gains, but some might do it for self-satisfaction or popularity, such as the identity theft of celebrities.
Identity Theft Penalty Enhancement Act—Prohibits aggravated identity theft (i.e., using someone else’s identity to commit felony crimes such as immigration violations, Social Security benefits theft and domestic terrorism).
What is identity protection refers to the tools and practices used to safeguard your personal information from identity theft and fraud. It’s important because identity protection helps prevent criminals from misusing your data, monitors suspicious activity, and reduces the financial and legal risks associated with identity theft.