Why is Public WI-FI Insecure?
- Even if the public WiFi connection you connect to may use encrypted protocols, nearby cafés, restaurants, airports, and other public places do not necessarily have the most secure Wi-Fi configurations, which is used to protect you against malicious entities online.
- Public Wi-Fi hotspots are littered with hackers, cybercriminals, and evil threat actors who are constantly finding effective ways to access your information.
- Since the vast majority of public Wi-Fi networks do not employ passwords, this leaves an open door for infiltrators to come and seize control of your online activities or gather sensitive data, like your personally-identifying information.
- It is relatively easy for snoopers to eavesdrop on your online activities and install spyware software, which gives them unfettered access to everything about you.
- What does this mean for you? You are prone to become a victim of identity theft which can be very costly.
How does PureVPN Protect Your WiFi?
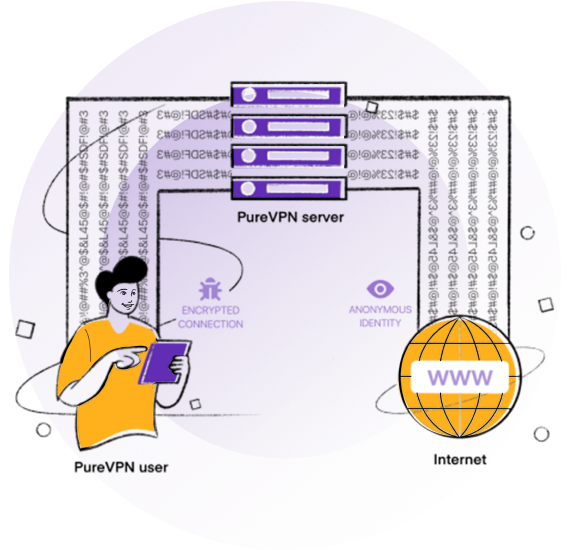
Upon connecting to PureVPN, all your data is sent through an encrypted tunnel, which makes it close to impossible to decipher or intercept. Moreover, your IP address is replaced with one from our VPN servers, allowing you to browse with a cloak of anonymity on any Wi-Fi network.
Why Use a VPN For WiFi?
Security on Public Wi-Fi Networks
A VPN will secure your online activities through its AES 256-bit encryption.
Work or Study Remotely
Students and remote workers can get past region locks instantly.
Instant Access to Other Countries
Get unrestricted and swift access to content from other countries.
Secure Banking over Public Wi-Fi
Access online banking and make secure financial transactions.
Access Social Media on Free Wi-Fi
Access your social accounts without having someone spy on your activities.
Share Sensitive Data Online
Send and receive sensitive information files securely on the web.
Building a Private WiFi Network
It is recommended to have a private WiFi network with high-level security protocols such as WPA/WPA 2 in place making it relatively more secure when compared to public hotspots.
We recommend a VPN for your private connection for additional security.
- Get a wireless access point. 802.11ax is the latest router technology available.
- Change the router default settings by logging in via its admin panel.
- Select the network name which is also known as the SSID.
- Choose a channel. Mostly, people choose 6, but to avoid overlap with other nearby networks, you may wish to select channels 1 or 11.
- Set up a username and password to protect the security of your router and save your settings.

How To Secure Your WiFi Connection—Always
-
Sign Up and Download
Sign up to PureVPN, then download the app to your preferred device (mobile, tablet or laptop)
-
Connect to PureVPN
Open the app and hit Connect to establish an encrypted VPN connection
-
Browse in Security
Browse the web with confidence!
PureVPN WiFi Exclusive Features
Secure WiFi
All users can connect to any Wi-Fi with complete confidence and peace of mind
Split Tunneling
Get the freedom to distribute your internet traffic as you please between PureVPN and your ISP
VPN Hotspot
Transform your Windows device into a hotspot to secure all connected devices
Router Configuration
PureVPN is compatible with a wide range of routers to secure your home or office network
Internet Kill Switch
Use our fail-safe IKS feature to ensure your real online identity remains a secret even if you lose connection to the VPN
256-Bit Encryption
PureVPN uses bank-grade AES 256-bit encryption to secure your Wi-Fi network traffic
How To Check Your New IP Address
All you have to do is follow these steps:
With PureVPN turned off, visit our What Is My IP page and check your IP address.
- Note down your real IP address.
- Open PureVPN app/software.
- Select your preferred server and hit “Connect”.
- Once your VPN connection is established, refresh or revisit our What Is My IP page and check your IP address – it should be different now!
- Set up a username and password to protect the security of your router and save your settings.
Frequently Asked Questions
-
Is using a VPN illegal?

Nope. In the vast majority of countries, using a VPN is perfectly legal, and it is even recommended if you are working with important or sensitive information. Many large companies use VPNs to provide an encrypted connection for employees working remotely. This question still comes up pretty often, though. The reason is that in the past, many hackers and other criminals used VPNs, and so using a VPN gained an association with illegal activity. Today, VPNs are used for precisely the same reasons that hackers used them in the past: they provide a secure, anonymous, encrypted connection for all your data. This said if you are travelling it is worth checking if the country you are in allows you to use your VPN. Better to be safe than sorry.
-
Can You Be Hacked Using a VPN?

A VPN safeguards data in transit between your device and the remote server, but you can get hacked despite its use. PureVPN employs AES 256-bit encryption on all of its connections, which is used by governments, banks, and law enforcement agencies across the world. This means that nobody will be able to get their hands on your passwords, credit card numbers, emails, photos, or anything personally identifiable (or not). While your internet connection, then, is relatively bulletproof, hackers are still capable of getting into your computer or mobile device; all they would have to do is trick you into installing malware. In other words, our internet connection is protected, but we’re our own weakest defense. That’s why we recommend using a strong antivirus program in conjunction with PureVPN.
-
Does a VPN Prevent Spying?

Since a VPN conceals your real Internet Protocol (IP) address with one from its servers, you can prevent third-parties like your ISP and the government from spying on you. They won’t be able to tell your real identity, what you’re up to online, and where your traffic is originating from. So to answer the question: yes, a VPN prevents snooping!
-
Can You Put a VPN on a Smart TV?

Setting up the VPN on your home router is the easiest method to enjoy VPN-protection on all devices, including your smart TV. However, if you can access the Google Play Store, and the VPN service offers a dedicated app, you can install it directly on your smart TV as well.
-
Can My ISP See My Browsing History with a VPN?

With your IP address hidden and data encrypted, you make it impossible for ISPs to see your browsing history and link those activities back to you. They will know you’re tunneling your traffic through a VPN, but they won’t be able to see what websites you’re visiting, which files you’re downloading, the services you’re using, or anything else. Your connection is completely secure.