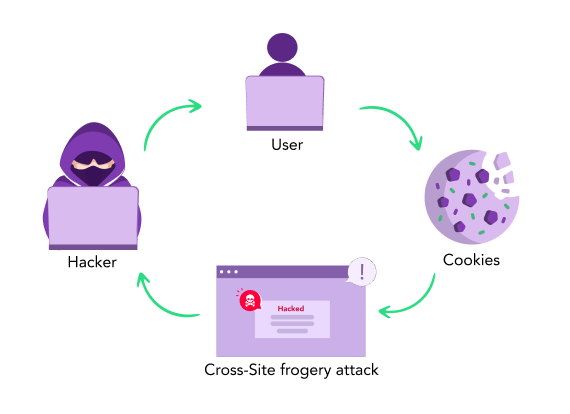
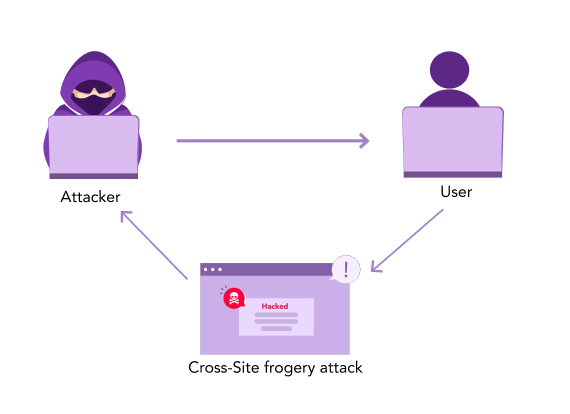
Cross-Site Forgery Attack
CSRF can be described as an attack that compels a user logged in to a web application into performing some negative actions. An attacker can employ a minimal level of social engineering to persuade users of an online app to carry out their desired activities (for example, by delivering a link via chat or email, etc.). It is a flaw in online security that enables an attacker to trick people into taking activities they did not want to carry out. Also, it allows the attacker to partially utilize the same origin policy, which is meant to stop various websites from meddling with one another. If the target is a frequent app user, a successful CSRF attack might compel them to carry out state-changing operations like money transfers, email address changes, and other such tasks. The entire web application may be compromised by CSRF in case the attack is made on an admin account.
How is a CSRF attack constructed?
It might be difficult to manually create the HTML required for a CSRF attack, especially when the necessary request has several parameters or other peculiarities. The use of Burp Suite Professional’s included CSRF PoC generator is the most straightforward approach for constructing a CSRF exploit:
-
Choose Engagement tools/Generate CSRF PoC from the right-click context menu.
-
Except for cookies, which the browser of the victim would automatically add, Burp Suite would produce specific HTML that will cause the chosen request to be sent.
-
To fine-tune the attack’s specifics, you may change a number of settings in the CSRF PoC generator. This may be necessary for certain odd circumstances to address requests’ peculiar traits.
-
To verify if the required request has been successfully made and the necessary action takes place, copy the produced HTML into a web page, check it in a browser that has been logged into the vulnerable website, and then complete the test.
What are CSRF tokens

A CSRF token can be referred to as a unique, unexpected value produced by the server-side app and provided to the client as part of the client’s HTTP request.
The server-side program verifies that the request includes the unique token that was supplied when the client initiated it and rejects the request in case of not receiving it.How does CSRF work?
- A pertinent act. The attacker has a motive to force a specific action in the app. Any attack on the user-specific data, like altering the user’s password, may fall under this category. It may also be a privileged action, like changing permissions for other users.
- Management of sessions using cookies. At least one HTTP request must be sent to complete the activity, and the application only uses session cookies to identify who is responsible for the requests. No other system exists to keep track of sessions or verify user requests.
- There are no unusual request parameters. There aren’t any parameters in the requests that carry out the action whose values can’t be discovered or predicted by the attacker. For instance, the function that forces a user to change their password is secure even though an attacker has to be aware of the current password’s value.
Example:
Rose wants to send $1000 to Steve using the CSRF-vulnerable bank.com online service. Attacker Cynthia intends to deceive Rose into transferring the money to Cynthia rather than herself.
The following steps make up the attack:
- Creating an exploit script or URL or script.
- Making Rose execute the action through social engineering.
Now, Cynthia chooses to use Rose as her victim to take advantage of this web app vulnerability, i.e., it being designed only to use GET requests.
Thus the exploit URL would be initially created by Cynthia, and it would transfer $100,000 from Rose’s account to her own.
Cynthia uses the original command URL, changes the beneficiary to herself, and dramatically increases the transfer amount:
When Rose is signed into the bank app, the social engineering component of the attack deceives her into loading the fake URL.
Typically, either she sends an unwanted email that contains HTML code placing an exploit script or URL on websites that the victim might be visiting when they are simultaneously using the online banking app.
The exploit URL may be shown as a regular link to entice the victim to be clicked or as a fake picture with the size of 0x0.
Rose will not see anything in case the email had this picture tag. Even if there is no visible proof that the transfer has occurred, the browser will send the request to bank.com.
An actual case of a CSRF attack employing GET on an application was a 2008 uTorrent vulnerability widely exploited for downloading malware.
How to prevent CSRF attacks?
- High entropy and unpredictable, just generally for session tokens.
- Associated with the session of the user.
- Strict validation in every situation before the appropriate action is carried out.
SameSite cookies are an extra CSRF protection that is only marginally useful and could be utilized along with CSRF tokens.
Other than this, using a VPN will also help you to hide your IP address. So that you are safe from these cyber attacks.
Conclusion
The internet can be a dangerous place for the vulnerable. And it is always a good idea to use VPN to protect yourself from carrying out negative activities via CSRF attacks.
Learn more about DDoS
- What is a DDoS Attack?
- How to Prevent DDoS Attack on Xbox
- Blackhole Routing
- HTTP Flood Attack
- Cross site Forgery Attack
- Malicious Payload
- HTTP Vulnerability
- What is Password Spraying
- DNS Flood Attack
- Low and Slow Attack
- What Happens During a DDoS Attack
- SSDP DDoS Attack
- Smurf DDoS Attack
- DDoS Botnets
- UDP Flood Attack
- Slowloris Attack
- NTP Amplification Attack
- DDoS Mitigation
- Ping Flood Attack
- DDoS Booter
- DNS Amplification Attack
- Brute Force Attack
- Golden Ticket Attack
- Credential Stuffing Attack
- How to Prevent DDoS Attack on Router
- Memcached attack
- Application Layer DDoS Attack
- DDoS Attack Prevention
- BGP Hijacking
- IP Fragmentation Attack